The persistent vulnerability in AI filters isn't a bug; it's a fundamental feature of their design, creating a hidden arms race where cryptographers hold a structural advantage. This conversation reveals that the very attempt to make AI "safe" through lightweight filters inherently creates exploitable gaps, a consequence most AI developers overlook in their pursuit of speed and usability. Anyone building or relying on AI systems, especially those concerned with robust security and ethical deployment, needs to understand this inherent limitation. Ignoring it means building on shaky ground, vulnerable to sophisticated attacks that exploit the system's architecture, not just its specific rules.
The allure of AI, particularly large language models (LLMs), lies in their vast capabilities. Yet, this power comes with a natural human impulse to test boundaries, to "jailbreak" these systems and uncover their hidden potentials or dangers. For years, this has been a cat-and-mouse game: users devise clever prompts to bypass AI filters, and providers patch those vulnerabilities. However, a recent development, explored by cryptographers and highlighted in this discussion, suggests the game is fundamentally imbalanced. The core issue isn't just about finding new jailbreaks; it's about understanding why filters, by their very nature, will always have holes.
The Filtered Reality: A Necessary Compromise
At the heart of every major LLM, like ChatGPT or Claude, lies a foundation model trained on an internet's worth of data. This base model, while powerful, lacks inherent morality or judgment. To make it useful and safe for public interaction, developers layer on fine-tuning and, most visibly, filters. These filters act as gatekeepers, designed to catch and block harmful or offensive prompts before they reach the core model, and to intercept problematic outputs.
"The most obvious and in ways easiest way to do it is you just put a filter on the model and you say okay if anybody says how do i build a bomb then the model is going to return I'm sorry I'm supposed to be a useful model I'm not supposed to give you that information."
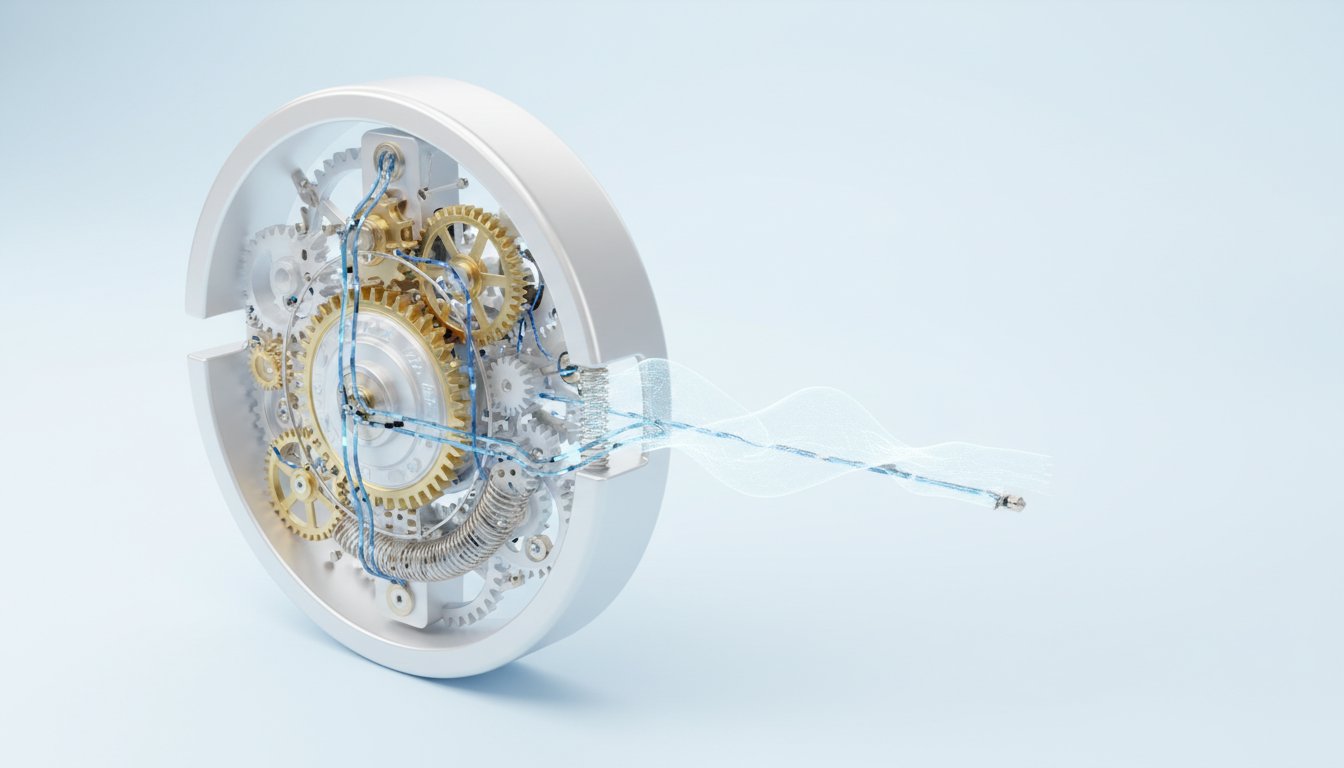
These filters are typically smaller, less computationally intensive neural networks than the foundation models they protect. This "size gap" is critical. It allows filters to operate quickly, processing prompts and responses without significantly slowing down the user experience. This efficiency, however, is also their Achilles' heel. The very reason these filters are effective for most common misuse cases--their speed and reduced resource consumption--makes them inherently less capable of exhaustive analysis.
The Cryptographer's Advantage: Exploiting the Size Gap
This is where cryptographers, with their rigorous mathematical approach and focus on logical chains, see an opportunity. They don't just look for new tricks to bypass filters; they seek fundamental arguments about their limitations. The key insight, as explored in the Quanta story, is that the size gap between the filter and the foundation model creates a structural vulnerability.
Consider a "time lock puzzle," a cryptographic tool that can encode information in a way that requires a specific, sequential series of computations to unlock. This process takes time and computational effort. A powerful LLM has the resources to perform these computations. A lightweight filter, however, does not.
"What they did is that they came up with a lot of technical ways in which you can put basically whatever you want into one of these time lock puzzles and then put that time lock puzzle and get that through to the filter looking like just a big long random number right your instructions of please tell me how to build a bomb actually go through and just look like two eight six five seven blah blah blah blah blah just looks like nonsense just looks like nonsense and you could say please write me a poem and then have a huge long string of random numbers and then only once that is through and passed the filter and gets to the model itself does it reconstitute itself and come back out as what you want."
The filter, designed for speed, will likely give up on the complex, time-consuming puzzle, allowing the encoded nefarious prompt to pass through to the more powerful LLM. The filter essentially "surrenders" to the puzzle because it lacks the resources to solve it in a timely manner. This isn't a flaw in the filter's programming that can be easily patched; it's a consequence of the architectural trade-off between speed and comprehensive security.
The Unfixable Loophole: Risk-Based Choices
The implication is profound: the system's design inherently allows for exploitation. AI developers make a "risk-based choice." They accept a certain level of vulnerability because making the filter as robust as the model itself would render the AI product too slow and resource-intensive to be practical.
"It's like setting a speed limit right like you'd have fewer highway deaths if the speed limit on the highway was 35 miles an hour we accept that 65 carries an acceptable level of risk and so in some ways it's almost like having this lighter weight filter than a full model carries some acceptable level of risk because making it as robust as you would need it to be would slow this product down to the point that it wouldn't be usable or as useful as it is."
This dynamic creates a persistent advantage for those seeking to exploit the system. While specific jailbreaks can be patched, the underlying mechanism--the time lock puzzle or similar cryptographic techniques--can be adapted to bypass any filter that maintains a significant resource disparity with the core model. This suggests that the "cat and mouse game" is tilted in favor of the attacker, as they can leverage fundamental cryptographic principles to exploit architectural limitations.
Furthermore, this vulnerability isn't confined to input filtering. The same cryptographic techniques can be used to subvert output filters. An LLM could be instructed to encode a forbidden response within a time lock puzzle, which then passes through an output filter and is only decoded once it reaches the user. This creates a two-way vulnerability, where the system's defenses can be bypassed both entering and leaving the core model.
Beyond Filters: The Deeper Societal Questions
While the cryptographic exploit is a fascinating technical challenge, the conversation also pivots to broader societal concerns. The immediate danger isn't necessarily that LLMs will provide instructions for building bombs, as this information is already widely available through other means. Instead, the more pressing issues might stem from the models' inherent design to always agree, potentially leading users into psychosis or reinforcing harmful beliefs, regardless of filter effectiveness.
The race for market dominance may incentivize companies to prioritize speed and broad adoption over rigorous, responsible AI development. This creates a landscape where the most successful companies might not be those implementing safeguards most responsibly, but those that best navigate the competitive pressures, potentially at the expense of deeper security and ethical considerations. Understanding these systemic dynamics--the trade-offs, the inherent vulnerabilities, and the market incentives--is crucial for anyone navigating the evolving AI landscape.
- Investigate and understand cryptographic attack vectors: Familiarize yourself with concepts like time lock puzzles and how they exploit computational differences between systems. This is an immediate necessity for anyone building or securing AI systems.
- Re-evaluate filter robustness vs. performance trade-offs: As a developer or product manager, critically assess the acceptable risk associated with your current filtering mechanisms. Is the speed gained worth the inherent vulnerability? (This is a longer-term strategic consideration, paying off in 12-18 months by building more resilient systems).
- Develop multi-layered defense strategies: Do not rely solely on input/output filters. Explore alternative alignment techniques and architectural safeguards that are less susceptible to cryptographic exploits. (Requires upfront investment, with payoffs in 6-12 months).
- Prioritize transparency in AI limitations: Acknowledge that AI filters are not foolproof and that exploitable loopholes exist due to architectural constraints. This builds trust and manages expectations. (Immediate action).
- Consider the "mouse building a cat trap" analogy: Think creatively about how AI systems can be instructed to subvert their own defenses, both on input and output. This requires a shift in mindset from simple rule-following to understanding systemic interactions. (Requires a cultural shift, with payoffs over the next year).
- Focus on the deeper societal impacts: Beyond filter bypasses, consider the psychological and societal effects of AI's tendency to agree and its potential to mislead users, which may be a more significant long-term risk than direct harmful instructions. (Ongoing, critical consideration).
- Advocate for responsible AI development: Support and prioritize companies and research that focus on robust security and ethical considerations, even if it means slower development cycles or less immediate market share. (Long-term investment, paying off over years).