The year is 2026, and the race is on to deploy AI agents. While the promise of agentic workflows offers unprecedented efficiency, the underlying security and identity challenges are far more complex than initially anticipated. This conversation with Ian Livingstone, CEO of Keycard, reveals how the transition from simple copilots to autonomous agents introduces profound risks, particularly around access control and data leakage. The hidden consequence isn't just about prompt injection, but a fundamental redefinition of trust and accountability in a world where compute itself becomes an actor. Enterprises, driven by the urgent need for operational efficiency and competitive defensibility, will lead this adoption, forcing security teams to enable rather than block, creating a critical need for robust, dynamic identity and access management solutions. Anyone building or deploying AI agents, from developers to CISOs, will gain a crucial understanding of the security landscape and a roadmap for navigating it safely.
The Unseen Architectures of Agentic Trust
The advent of AI agents is not merely an upgrade to existing software; it represents a paradigm shift in how we interact with and delegate tasks to computing systems. As Ian Livingstone articulates, we are moving along a continuum from AI assistance, like advanced autocomplete copilots, to truly autonomous agents capable of executing complex, multi-step tasks with minimal human oversight. This evolution, while promising immense productivity gains, introduces a cascade of security and identity challenges that current frameworks are ill-equipped to handle. The critical, often overlooked, consequence is the fundamental redefinition of trust and accountability.
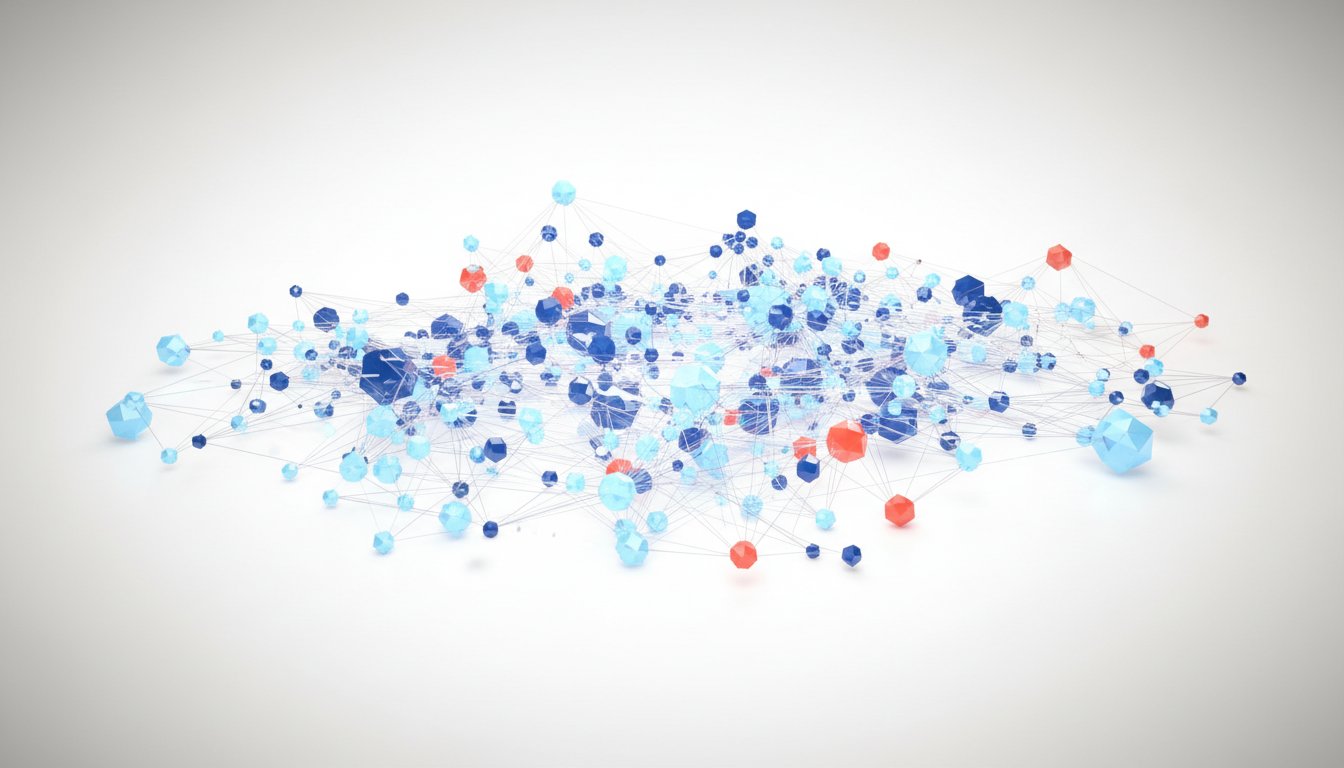
The initial security incidents, like the one described involving a company’s SaaS service, highlight a glaring vulnerability: the failure to properly manage authentication and authorization for agents. When an agent, designed to query internal data, can inadvertently serve data from other firms simply by a user asking for "my data," it reveals a critical breakdown in identity and access control. This isn't a simple bug; it’s a systemic flaw in understanding how agents operate within complex, multi-party relationships. The traditional perimeter-based security models, which relied on static user roles and group memberships, are rendered obsolete.
"The fundamental challenge is, you know, when we went and solved user federation, we never had to solve what fundamentally under the hood problem this is, which is now we have a piece of compute that we need to be able to federate across cloud and across, you know, network and companies."
-- Ian Livingstone
The core issue is that agents, unlike static user accounts, are dynamic entities that require context-aware access. An agent might need to access sensitive production data to perform a task, but that access must be strictly scoped to the user’s intent and permissions. The ability for an agent to, for example, access production data and then use a web browser to query that data, potentially exposing it, creates a complex web of authorization. This isn't just about preventing malicious actors; it's about ensuring that even well-intentioned agents operate within defined boundaries, preventing accidental data leakage or unauthorized actions. The problem is compounded by the fact that agents often interact with multiple tools and downstream resources, creating a complex, ephemeral, and hyper-contextual access landscape.
This shift from static access control to dynamic, task-based policies is where conventional wisdom fails. The assumption that existing standards like OAuth are sufficient is challenged by the multi-tenancy and actionability of agents. Livingstone points out that while protocols like MCP (Multi-cloud Credential Provider) and A2A (Agent-to-Agent) attempt to address aspects of agent management, they often fall short of providing a unified, secure framework. MCP, for instance, can lead to "secret sprawl on steroids," where production credentials are run on local machines with little control, blurring the lines between user identity and agent identity. This unseen risk, where an agent might have broad production access without clear differentiation from its user, is a ticking time bomb.
"My core challenge is I can't differentiate between these two things, and this is unseen risk."
-- Ian Livingstone
The value creation of an agent, Livingstone argues, isn't solely in the underlying model but in the context and tools it can access at runtime. This necessitates a complete reinvention of the trust equation. Instead of trusting a user based on their static role, we must trust an agent based on its dynamically granted permissions for a specific task. This requires a move towards task-based, intent-based policies that are enforced downstream. The implications are vast: organizations must consider not only how their agents interact with internal data but also how they become agents themselves, interacting with customers and partners in this new ecosystem.
The urgency for enterprises to adopt agents is driven by a dual imperative: operational efficiency and competitive defensibility. The ability to freeze headcount while increasing productivity, as seen with coding agents, is a compelling business case. Furthermore, companies risk being disintermediated if they cannot adapt to a future where shopping, software interaction, and workflow automation are primarily agent-driven. This pressure means that security teams, historically gatekeepers, are now tasked with enabling these initiatives safely. The "empire of no" is crumbling under the weight of business necessity, forcing a pivot towards secure enablement.
Key Action Items
-
Immediate Action (Next Quarter):
- Inventory Agent Deployments: Identify all current and planned AI agent deployments within the organization.
- Map Agent Access: For each agent, explicitly document the data, tools, and systems it accesses.
- Review Existing Credentials: Audit how production credentials are being managed and accessed by agents, particularly in development and testing environments.
- Develop Pilot Task-Based Policies: Select a low-risk agent and define granular, task-specific access policies for its operations.
-
Medium-Term Investment (Next 6-12 Months):
- Implement Dynamic Access Control: Invest in solutions that can enforce context-aware, intent-based access policies for agents at runtime.
- Establish Agent Identity Framework: Develop a clear framework for identifying, authenticating, and authorizing agents distinctly from their users.
- Integrate Auditing and Monitoring: Ensure robust logging and monitoring are in place for all agent actions, providing clear audit trails.
-
Longer-Term Investment (12-18 Months and Beyond):
- Build Agent Governance Strategy: Create a comprehensive strategy for governing the lifecycle of AI agents, including their development, deployment, monitoring, and retirement.
- Explore Federated Agent Solutions: Investigate and adopt solutions that interoperate with open standards for agent management and security, ensuring flexibility and avoiding vendor lock-in.
- Develop "Agentic" Business Processes: Proactively redesign core business processes to leverage agent capabilities, focusing on areas with high potential for operational efficiency and competitive advantage.