The Microsoft Authenticator app's decision to delete Entra credentials on rooted or jailbroken devices is more than just a technical change; it signals a broader shift towards device-level control that has significant, often overlooked, implications for user autonomy and organizational IT strategy. This conversation with the 2.5 Admins podcast reveals how seemingly straightforward security measures can cascade into complex problems, particularly concerning multi-factor authentication (MFA) recovery and the hidden vulnerabilities of everyday vehicle technology. Anyone managing IT infrastructure, or even just a personal digital life, needs to understand these downstream effects to avoid costly lockouts and privacy erosion. This analysis highlights why conventional wisdom about security and convenience often fails when confronted with the reality of complex systems and vendor control.
The Unintended Lockout: MFA's Broken Recovery Chains
The most immediate and visceral consequence of the Microsoft Authenticator policy, and indeed many modern MFA systems, is the potential for complete lockout when a user loses access to their primary authentication device. Jim's nightmare experience with a client losing their phone and subsequently being unable to regain access to their Microsoft Entra account is a stark illustration of this systemic failure. The core issue isn't the MFA itself, but the broken and inaccessible recovery workflows designed to circumvent such scenarios.
The podcast highlights a fundamental flaw: the very systems designed for security often lack robust, user-accessible pathways for recovery. FAQs and support documentation invariably point to disabling MFA through an administrative interface, a step that's impossible when the administrator is the one locked out due to a lost device. This creates a Catch-22 where the security measure designed to protect the account also serves as an insurmountable barrier to regaining access.
"Log into the panel with your admin account and disable MFA and then re-enable it." Well, how do I do that, genius, when I can't log into the admin account because it requires MFA that was never enabled in the first place?
This highlights a critical systems thinking failure: optimizing for the "happy path" of secure access while neglecting the "unhappy path" of recovery. The downstream effect is not just user frustration, but prolonged downtime--in Jim's client's case, over two weeks without email access. This is compounded by the fact that direct human support is increasingly difficult to access, forcing users through automated systems or, as Jim discovered, navigating to accounts receivable to find a human capable of opening a support ticket. The implication is that even services marketed for their ease of use require a sophisticated IT professional to manage them safely, undermining the "cloud is easy" narrative.
The Slippery Slope of Device Sanctioning and the Illusion of Choice
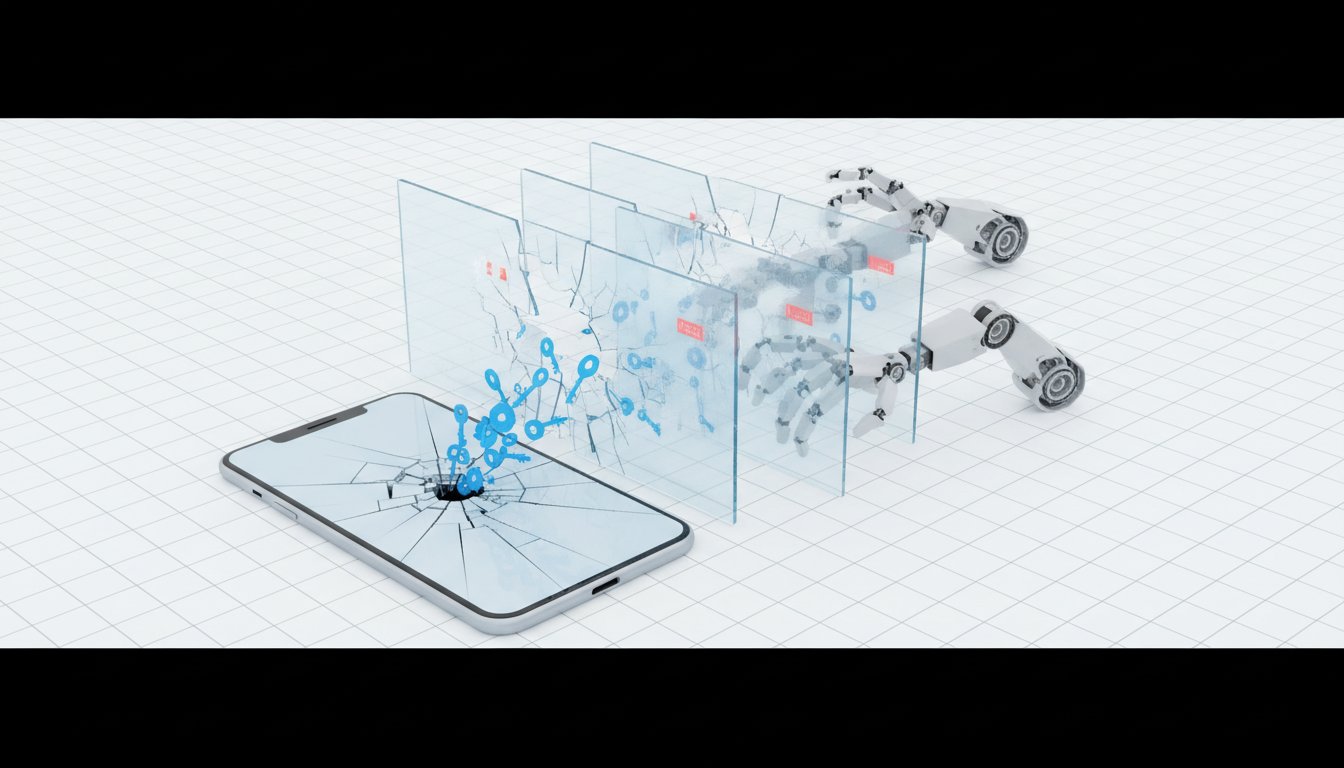
Microsoft's decision to delete Entra credentials from rooted Android phones or jailbroken iPhones, while framed as a security measure, represents a significant escalation in vendor control over user devices. Alan and Jim discuss how this aligns with a long-standing trend, reminiscent of Microsoft's Palladium initiative, to lock down devices to company-approved configurations.
The non-obvious consequence here is the erosion of user autonomy. Users who choose to modify their devices for enhanced control, privacy, or functionality are effectively being punished and locked out of services. While one host suggests this could be a useful option for admins to choose to enforce, the podcast emphasizes that Microsoft is imposing this policy unilaterally. This creates a dynamic where users must either comply with vendor dictates or risk losing access to essential services.
This is the same shit Microsoft has been pushing since literally the late 90s with the Palladium initiative. They have been trying to lock down all devices to only be in a company-approved configuration, regardless of what the users want, for literal decades.
The implication is that "your device" is increasingly becoming "the company's device" when it comes to accessing corporate resources. This has a chilling effect on device customization and shifts the balance of power further towards service providers. The advantage for organizations that embrace this trend might be a perceived increase in security, but the long-term cost could be a less adaptable and more controlled user base, potentially stifling innovation and user satisfaction.
Tire Pressure Sensors: The Invisible Tracking Network
The discussion around vehicle tire pressure sensors (TPMS) reveals a fascinating and unsettling consequence of ubiquitous, unencrypted wireless communication: silent, widespread tracking. The fact that these sensors broadcast unique identifiers (GUIDs) in the clear, mandated for safety, creates an unintended, pervasive tracking mechanism.
When vehicles pass by devices capable of intercepting these signals--even inexpensive ones--their unique identifiers can be logged. Over time, this data can be correlated to map vehicle movements with remarkable accuracy. This isn't theoretical; the podcast mentions studies where researchers tracked vehicles using $100 devices from 40-50 meters away.
What that means is if you happen to be in control of devices that are near enough to a roadway to intercept the tire pressure sensors as vehicles go by... all of your devices are uniquely identifiable by these tire pressure sensor signals that they're broadcasting all the time. So if you can intercept those signals, you can track where cars go.
This is a prime example of a system designed for one purpose (safety) having a significant, unaddressed second-order negative consequence (tracking). The analogy to Wi-Fi MAC address randomization or Bluetooth tracking is apt, but TPMS operates on a more fundamental, less controllable level for the average user. The podcast points out that disabling these sensors would compromise vehicle safety functionality, making them unavoidable tracking beacons. The advantage of this knowledge lies in understanding the pervasive nature of data collection; even seemingly innocuous vehicle components contribute to a larger surveillance infrastructure. The failure here is in not considering the broadcast range and unique identification requirements in the context of potential misuse, leading to a system where privacy is an afterthought.
ZFS Snapshots and the Fragility of Replication Chains
The "free consulting" segment delves into the intricacies of ZFS replication, particularly concerning cold storage and broken snapshot chains. Chad's scenario of needing to use a ZFS mirror with one disk removed due to faulty RAM, and Joe's problem of having pruned old snapshots on a cold backup drive, both illuminate the critical dependency on common starting points for incremental replication.
The core insight is that ZFS incremental replication relies on identifying a common snapshot or bookmark. If that common point is lost--either by removing a disk from a mirror (which ZFS can handle by replaying logs or resilvering) or by pruning old snapshots on a backup target--the replication chain is broken. The immediate solution is a full re-replication, which can be time-consuming and resource-intensive.
If you don't have a snapshot or a bookmark in common, then yeah, a full replication is the only way to begin again.
The podcast offers a crucial workaround: ZFS bookmarks. Unlike snapshots, bookmarks are lightweight and don't consume significant space. They serve as pointers to specific transaction groups (TXGs) from past snapshots, even if the snapshot itself has been pruned. By creating bookmarks of recent common snapshots before a target drive goes cold or before pruning occurs, users can maintain a viable replication chain. This highlights a delayed payoff: the small effort of creating bookmarks upfront prevents a potentially massive effort of full re-replication later. The conventional approach of relying solely on snapshots, and then pruning them aggressively, fails to account for the long-term need for incremental replication starting points, especially for cold storage. The "competitive advantage" here comes from understanding and implementing ZFS bookmarks, a less obvious feature that ensures long-term data synchronization efficiency.
Key Action Items
- Implement ZFS Bookmarking for Cold Storage: Proactively create ZFS bookmarks for your most recent common snapshots on all cold backup targets. This is a low-effort, high-reward action that prevents costly full re-replications down the line. Action: Immediately. Payoff: Prevents future data sync issues, potentially saving days of work.
- Establish Multi-Admin Accounts for Critical Services: For any service with MFA (e.g., Microsoft Entra, Google Workspace), ensure at least two administrator accounts exist, each with independent MFA methods. This prevents a single point of failure, like a lost phone, from causing complete lockout. Action: Within the next quarter. Payoff: Immediate security resilience, prevents extended downtime.
- Review MFA Recovery Procedures Regularly: Don't just set up MFA; periodically test your recovery process. This includes verifying access to backup codes, secondary devices, or alternative authentication methods. Action: Quarterly. Payoff: Ensures recovery is possible when needed, reduces panic and downtime.
- Evaluate Device Compliance Policies Critically: Understand the implications of vendor policies that dictate device configurations (e.g., rooted/jailbroken detection). Assess whether the security benefits outweigh the loss of user control and potential for lockouts. Action: Within the next six months. Payoff: Informed decision-making regarding vendor lock-in and user flexibility.
- Consider TPMS Tracking Implications: Be aware that vehicle TPMS data is broadcast openly and can be used for tracking. For highly sensitive individuals or organizations, explore potential mitigation strategies if operating in high-risk environments. Action: Awareness is immediate; mitigation is situational. Payoff: Enhanced understanding of personal digital footprint.
- Document ZFS Mirror Maintenance Procedures: For systems using ZFS mirrors, document the exact procedure for handling disk failures or removals, including the role of ZFS's self-healing capabilities and the importance of not powering up the primary system while a mirror disk is absent. Action: Within the next month. Payoff: Clear guidance during stressful hardware failures, reduces risk of data corruption.
- Investigate Alternative MFA Solutions: If your current MFA solution has cumbersome or inaccessible recovery paths, research alternatives that offer more user-friendly and robust self-service recovery options. Action: Over the next 6-12 months. Payoff: Long-term reduction in support burden and user frustration.