2.5 Admins
By The Late Night Linux Family
2.5 Admins is a podcast featuring two sysadmins called Allan Jude and Jim Salter, and a producer/editor who can just about configure a Samba share called Joe Ressington. Every week we get together, talk about recent tech news, and answer some of your admin-related questions.
19 episodes
All Episodes
The Demise of General-Purpose Computing and Its Hidden Costs
Personal computing's flexibility is fading as systems become controlled appliances, demanding new strategies for system design and support.
View Episode Notes →
Hidden Costs of "Unlimited" Storage, Security Loops, and AI Code
Discover how seemingly simple tech choices create hidden costs, erode trust, and undermine security, offering a critical advantage in building resilient systems.
View Episode Notes →
Orbital Data Centers and AI Summaries: Hidden Costs of Convenience
Orbital data centers and AI summaries reveal how convenience masks profound challenges, proving that immediate gains often overshadow long-term sustainability and reliability.
View Episode Notes →
The Hidden Costs of Ease: Fragility, Lock-in, and Long-Term Value
Embrace upfront effort for long-term control. Choosing open-source and managing complexity now prevents costly lock-in and fragility later.
View Episode Notes →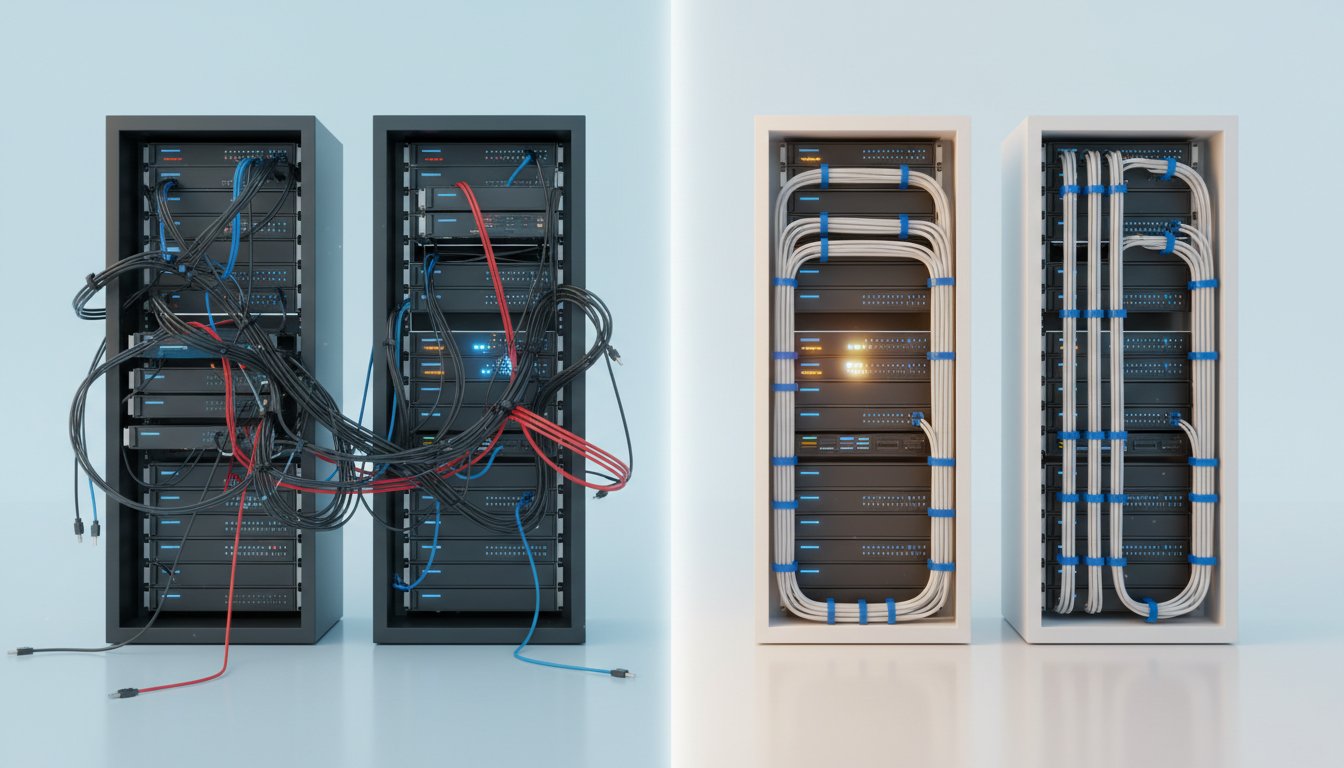
The Windows Update Paradox: Why "Less Rubbish" Isn't Good Enough
Windows updates are improving, but "less rubbish" isn't enough. Discover why a fundamental shift is needed to truly enhance user experience and system stability.
View Episode Notes →
Systemic Vulnerabilities Undermine Security and Trust
Discover how seemingly minor security flaws cascade into widespread compromise, undermining national security and revealing the hidden fragility of complex technological systems.
View Episode Notes →
Passkeys' Encryption Risk and Friction's Systemic Value
Passkeys, while convenient, risk locking you out of encrypted data if your primary device is lost. Explore resilient systems by embracing deliberate friction and unconventional solutions.
View Episode Notes →
Vendor Device Control and MFA Lockouts Create Systemic Risks
Vendor control over devices escalates, turning "your device" into "the company's device" and eroding user autonomy, while broken MFA recovery chains create costly lockouts.
View Episode Notes →
Unpacking Downstream Risks of Technological Innovations
Discover hidden risks in technological advancements. Understand how innovations create long-term problems and systemic vulnerabilities, offering strategic advantages to avoid costly pitfalls.
View Episode Notes →
Systemic Hard Drive Scarcity Fueled by AI Demand and Broken Pricing
AI workloads have outstripped hard drive production, creating systemic fragility, broken pricing, and a dangerous reliance on refurbished components.
View Episode Notes →
Hardware Performance Leaps Require Software Paradigm Shifts
Dual-actuator hard drives promise performance leaps, but success hinges on software adapting to hardware's complex demands, not just raw speed.
View Episode Notes →
Systemic Software Vulnerabilities: Update Mechanisms, AI Decay, and Data Resilience
Software update mechanisms are fragile, creating systemic vulnerabilities. Learn how to build robust systems that avoid the hidden costs of convenience and data decay.
View Episode Notes →
Centralization's Risks: Autodiscover Vulnerabilities and Cloud Trade-offs
Convenience often masks hidden risks in technology, from email protocol vulnerabilities to cloud data loss. Understand these trade-offs to build resilient IT infrastructure.
View Episode Notes →
Convenience Masks Vulnerability: Cloud, Encryption, and Data Ownership Risks
Convenience erodes data control and security, creating hidden vulnerabilities in cloud services and encryption. Understand these non-obvious risks to safeguard your digital life and assets.
View Episode Notes →
Hardware Fragility Demands Proactive Data Protection and Online-Dependent Systems
Windows activation demands online connection, malware exploits fake errors, and hardware failure is constant. Robust, automated backups are essential for data integrity.
View Episode Notes →
Vulnerabilities in Network Infrastructure and AI Expose Systemic Fragility
AI and network vulnerabilities expose critical risks, from Cisco router outages to data exfiltration via Microsoft Copilot, demanding robust safeguards.
View Episode Notes →
Email's Inherent Insecurity Fuels Impersonation Scams Over Technical Weakness
Email's inherent insecurity allows sophisticated scams to exploit trust, not technical flaws, leading to widespread fraud. Learn how to build defenses beyond technology.
View Episode Notes →
Expired Domains, LLM Bullshit, and Home Lab Performance Bottlenecks
Expired government domains become attack vectors, and LLMs generate plausible falsehoods by prioritizing patterns over truth, not deception.
View Episode Notes →
Iterative Documentation and Re-execution for Deep Sysadmin Skill Development
Documenting and rebuilding technical tasks from your own instructions builds deep, transferable sysadmin skills and creates a powerful portfolio for job interviews.
View Episode Notes →