Quantum Physics -- Not Math -- Secures Future Communications
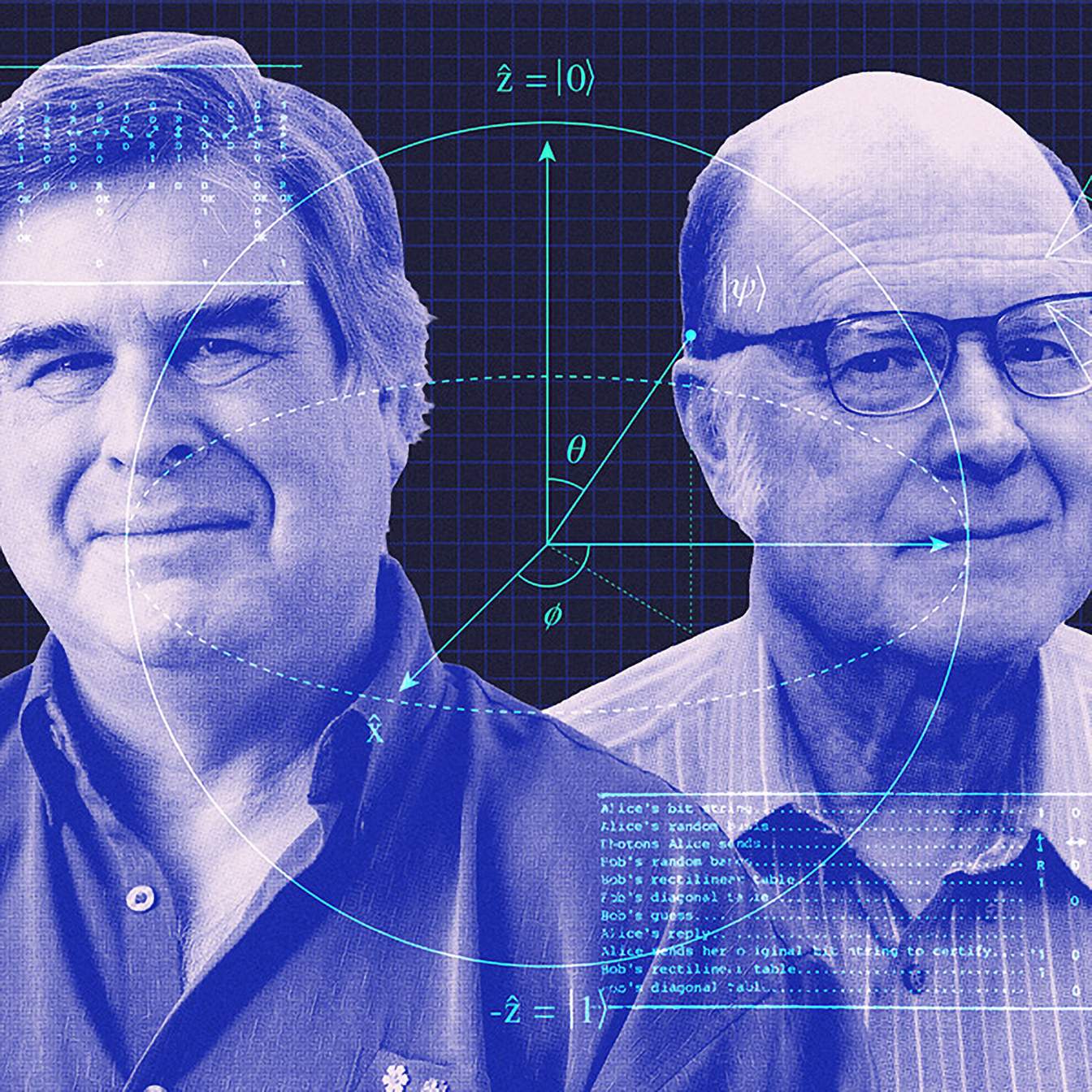
The quantum world offers not just a new paradigm for computation, but a fundamental re-imagining of digital security. This conversation with Ben Brubaker, detailing the foundational work of Charles Bennett and Gilles Brassard, reveals that the very laws governing the smallest particles hold the key to protecting our most sensitive information. The non-obvious implication is that the future of secure communication doesn't lie in more complex mathematics, but in the inherent, unbreakable physics of quantum mechanics. This is essential reading for anyone involved in cybersecurity, software development, or strategic technology planning, offering a glimpse into a future where quantum threats necessitate quantum solutions, providing a distinct advantage to those who understand this shift now.
The Unbreakable Foundation: When Physics Becomes the Ultimate Firewall
The prevailing wisdom in digital security often hinges on the complexity of mathematical problems. We rely on algorithms that are, in theory, too difficult for current computers to crack within a reasonable timeframe. However, this conversation with Ben Brubaker, discussing the groundbreaking work of Charles Bennett and Gilles Brassard, exposes a critical flaw in this approach: the advent of quantum computing. These machines, still in their nascent stages, possess the theoretical power to dismantle many of the mathematical fortresses we’ve built. The non-obvious consequence is that our current digital security infrastructure is, in essence, on a ticking clock.
Bennett and Brassard’s contribution, which earned them the ACM Turing Award, wasn't about finding harder math problems. Instead, they recognized a profound connection between quantum physics and cryptography. Their foundational work, dating back to the 1980s, laid the groundwork for quantum key distribution (QKD), a method that leverages the peculiar laws of quantum mechanics to secure communication. This isn't about making encryption harder to break; it's about making it impossible to break without detection.
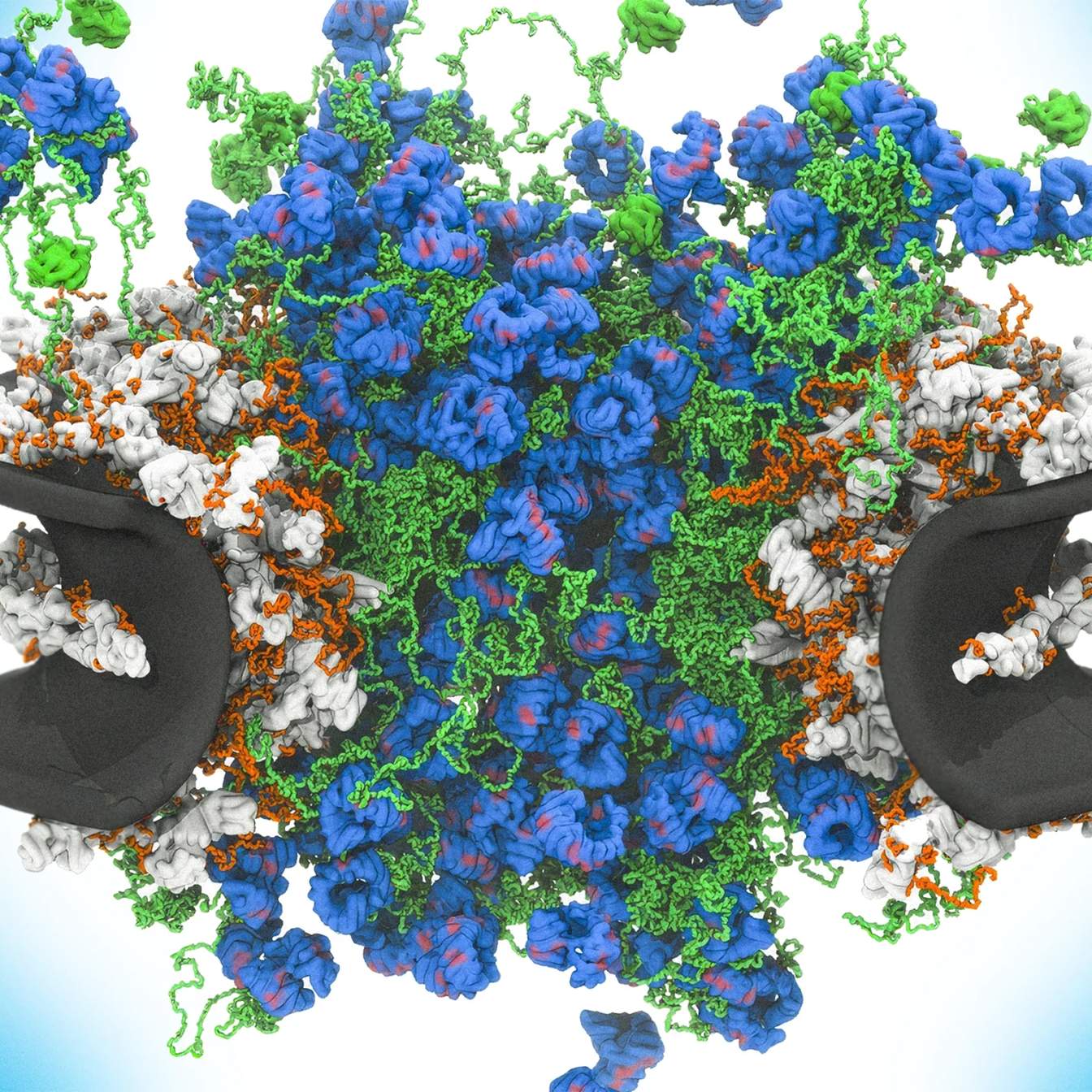
The core insight here is that information encoded in quantum systems, like the polarization of a photon, behaves differently when observed. Unlike classical information, which can be copied or read without altering its state, quantum information is inherently fragile. Any attempt by an eavesdropper to intercept and measure these quantum signals inevitably disturbs them. This disturbance, a direct consequence of quantum measurement disturbance, leaves a detectable "imprint" that the legitimate parties, Alice and Bob, can identify.
"The idea is that if you already knew something about how this information was encoded in these photons in the first place, if you knew what measurement to make, then you could safely extract this information, and you would do it without messing anything up. But if you don't know how the information is encoded, then you don't really know exactly what type of measurement to make, and you might make a measurement that instead of faithfully giving you whatever that information is that was encoded there, it will just screw up that information."
-- Ben Brubaker
This is where conventional wisdom falters. Traditional cryptography assumes that information can be passively observed. QKD, however, fundamentally alters this by making eavesdropping an active, detectable process. The immediate benefit of QKD is not just secure key distribution, but provable security. The delayed payoff, and the true competitive advantage, lies in building a communication infrastructure that is resilient to future threats, including those posed by quantum computers. While current encryption methods might still be adequate for today, the foresight shown by Bennett and Brassard anticipates a future where they will not be.
This leads to the second critical insight: the transition from computational security to physical security. For decades, we’ve relied on the assumption that certain mathematical problems are computationally intractable. Bennett and Brassard’s work shifts the paradigm. Instead of relying on what computers can't do, they leverage what quantum mechanics dictates. This is a critical distinction. It means that the security of communication is no longer a matter of computational difficulty, but a matter of physical law.
The initial concept of "quantum money," proposed by Stephen Wiesner and explored by Bennett, highlights this shift. The idea of a currency that cannot be counterfeited due to its quantum properties underscores that information itself, whether it’s a monetary value or a secret key, can be secured by physical principles rather than algorithmic complexity. This theoretical underpinning, initially met with skepticism, ultimately paved the way for QKD.
"The bank maybe knows exactly how each particle was set up and what measurements you would make, but the counterfeiter, without knowing this, would have to guess correctly how to measure each of this maybe long number of photons, and the chance that they'd be able to do this reliably is basically zero."
-- Ben Brubaker
The implications for long-term strategy are significant. Investing in QKD infrastructure, while potentially more complex and costly in the short term than implementing existing cryptographic protocols, offers a durable, physics-based security that is vastly superior. This is where immediate discomfort--the learning curve, the specialized hardware--creates a lasting advantage. Competitors who stick to computationally-based security will eventually find their defenses obsolete, while those who embrace quantum-based security will have built a moat that quantum computers cannot breach.
Finally, the narrative around QKD reveals a powerful lesson in innovation: the value of pursuing seemingly "kooky" ideas. Bennett and Brassard’s work was initially considered fringe. The community interested in quantum information science was small enough to fit in a single conference room. This highlights how groundbreaking advancements often arise from individuals who are willing to explore unconventional paths, driven by curiosity rather than immediate commercial pressure. The delayed payoff for their persistence was the creation of an entirely new field and a solution to a problem that hadn't fully materialized yet.
The challenge, as Brubaker points out, is that QKD doesn't offer a complete replacement for all aspects of public-key cryptography. It excels at key distribution but doesn't inherently solve the problem of sending encrypted messages without prior agreement over a single quantum channel. This necessitates parallel research into post-quantum cryptography, which explores alternative mathematical problems that quantum computers are believed to be unable to solve. However, the allure of QKD lies in its foundation on physical laws, offering a level of certainty that computational assumptions cannot match.
Key Action Items
-
Immediate Action (Next 1-3 Months):
- Educate Key Stakeholders: Conduct internal workshops to explain the impending threat of quantum computing to current encryption methods and the potential of quantum cryptography.
- Inventory Current Cryptographic Assets: Document all systems and data relying on public-key cryptography to understand the scope of the vulnerability.
- Begin Research into Post-Quantum Cryptography Standards: Familiarize teams with emerging NIST standards and other post-quantum algorithms.
-
Short-Term Investment (Next 3-9 Months):
- Pilot QKD Implementations: Explore small-scale pilot projects for highly sensitive point-to-point communication channels within your organization.
- Develop Hybrid Security Strategies: Integrate QKD or post-quantum cryptography alongside existing methods for a layered defense.
- Engage with Quantum Security Experts: Consult with specialists to assess your organization's specific risks and develop a tailored transition roadmap.
-
Longer-Term Investment (9-18+ Months):
- Develop a Phased Migration Plan: Outline a multi-year strategy for migrating critical systems to quantum-resistant encryption, prioritizing the most vulnerable assets.
- Invest in Quantum-Resistant Infrastructure: Begin allocating budget for hardware and software upgrades that support QKD or post-quantum algorithms.
- Foster Internal Expertise: Train security and development teams in quantum cryptography principles and implementation, creating a knowledgeable internal resource. This requires patience and a willingness to invest in foundational security, where discomfort now creates a significant advantage later.