Foundational Software Principles Solve Systemic Crises
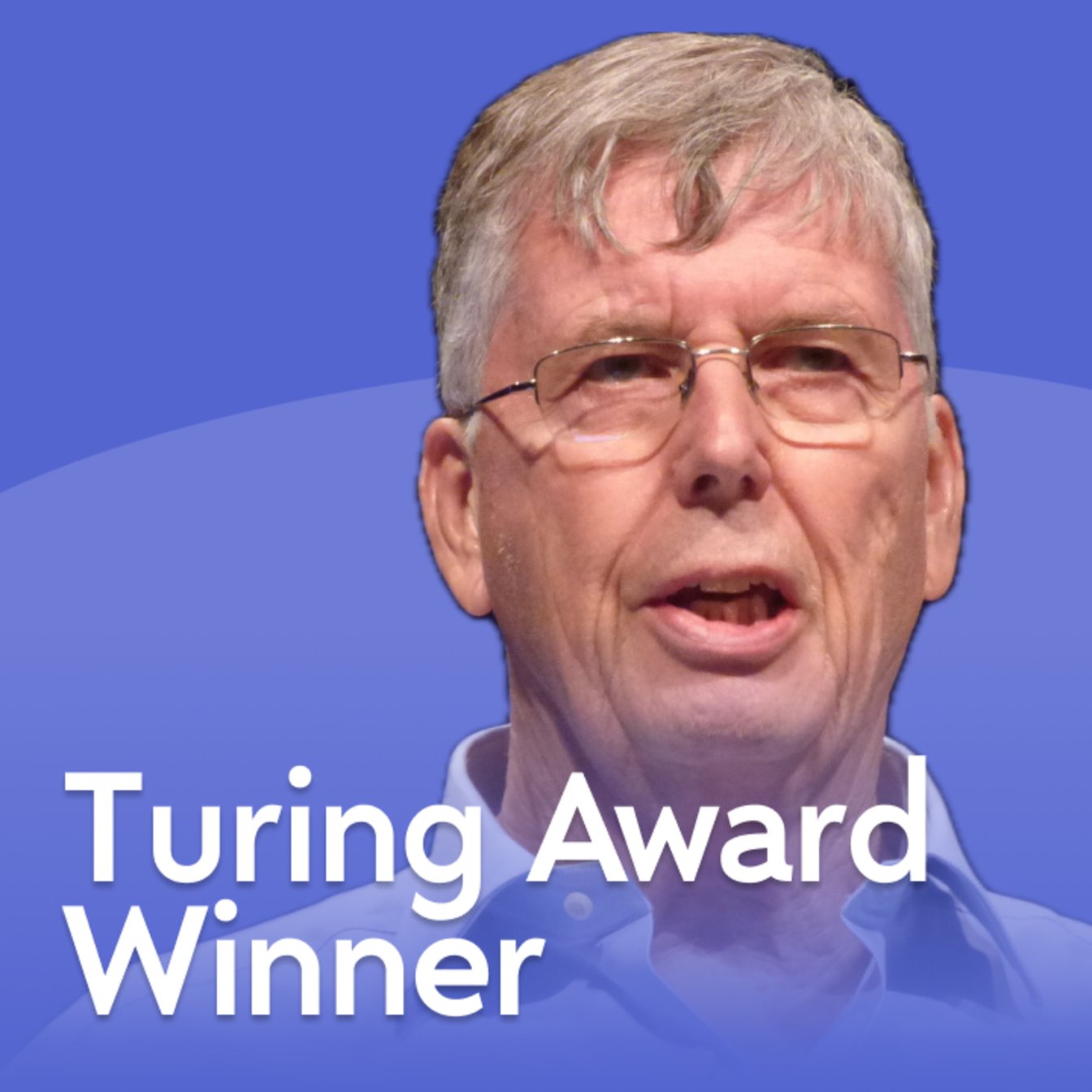
This conversation with Turing Award winner Barbara Liskov offers a profound look into the foundational principles of modern software engineering, revealing how seemingly abstract concepts like data abstraction and modularity were not merely academic curiosities but essential solutions to a widespread "software crisis." The non-obvious implication is that the very stability and scalability we take for granted in software today were hard-won battles against fundamental design flaws. This analysis is crucial for software architects, lead engineers, and CTOs who need to understand the long-term consequences of architectural choices, providing them with the foresight to build more robust and maintainable systems by embracing principles that, while sometimes difficult to implement initially, create durable competitive advantages.
The Hidden Costs of "Good Enough" Modularity
The 1970s software crisis wasn't a failure of individual programmers, but a systemic inability to build large, reliable software systems. Liskov pinpoints the core issue: a lack of true modularity. At the time, the primary mechanism was the procedure, ill-suited for complex entities like databases or file systems that aren't simple input-output operations. This forced teams into building monolithic, unmanageable codebases where a single bug could render millions of dollars and years of work useless.
Liskov's insight, born from practical necessity in a small team at Mitre, was the concept of data abstraction. This wasn't just about grouping code; it was about defining modules by their interface--what they do--while hiding the implementation--how they do it. This separation allows for reasoning about correctness module by module, a cornerstone of building complex systems. The CLU programming language, which she co-developed, was a direct manifestation of this idea, providing a concrete mechanism for abstract data types.
"The problem was that to get a big program that works, you need modularity, and you need to break your program up into small pieces. Each piece provides an interface with a hopefully complete description of what service it provides for you, and then inside is an implementation that's hidden, and nobody pays any attention to it on the outside."
This foundational work directly influenced later languages, including Ada and eventually Java, embedding the principle of encapsulation into mainstream programming. The contrast with Python, which Liskov notes lacks true encapsulation, highlights a persistent tension: the desire for flexibility can undermine the robustness that true modularity provides. Python's ease of use for beginners comes at the cost of allowing internal module details to be exposed and manipulated, a shortcut that can lead to cascading failures in larger, more complex projects. This is a classic example of a short-term gain (simplicity for naive users) leading to a long-term cost (reduced reliability and maintainability for complex systems).
The Unseen Battleground: Distributed Systems and Consensus
Liskov's transition into distributed computing in the 1980s tackled another frontier: building programs composed of pieces spread across multiple networked computers. The dream of distributed systems, as articulated by Bob Kahn, was compelling, but the reality was fraught with peril. How do you ensure that a computation spanning multiple machines either completes successfully everywhere or fails entirely, leaving no partial, corrupted state? This is the essence of distributed transactions, a problem Liskov addressed with the Argus programming language, borrowing concepts from database transactions.
This led to her seminal work on Viewstamped Replication, developed with Brian Oki. This protocol addressed the critical challenge of maintaining consistent data across multiple sites, ensuring availability even when some nodes failed. It was a precursor to modern cloud storage, providing a mechanism for data to be stored reliably across the internet. The core innovation was a consensus mechanism, not based on synchronized clocks, but on a simple, incrementing "view number" to track the state of the system and manage leader election.
"How do you have data out on the internet stored at multiple sites with correct behavior and always accessible as long as enough nodes are up and running and the network is working?"
This work, independently conceived by Leslie Lamport as Paxos, revealed a fundamental truth about distributed systems: achieving agreement (consensus) is incredibly difficult. While Viewstamped Replication and Paxos are essentially the same, Paxos gained wider recognition, perhaps due to its catchy name and Lamport's prolific dissemination through talks and papers. This is a powerful lesson: the technical merit of an idea is only part of the equation; how it's communicated and branded can significantly impact its adoption. The immediate payoff of these protocols was the ability to build more resilient systems, but the delayed payoff was the foundation for the highly available, fault-tolerant services that define the modern internet.
The Subtle Power of Behavioral Subtyping
The principles of object-oriented programming (OOP) were emerging concurrently with Liskov's work on data abstraction. While Alan Kay was developing Smalltalk on the West Coast, Liskov was working on CLU and Bill Wolf and Mary Shaw on Alphard on the East Coast. These were largely independent efforts, highlighting how foundational ideas can emerge from different contexts.
Liskov's contribution to OOP, the Liskov Substitution Principle (LSP), arose from her analysis of inheritance, a core tenet of Smalltalk. She observed that while languages supported subclasses inheriting from superclasses, the meaning of this relationship--specifically, the behavioral contract--was often unclear. Her work, formalized later with Jeannette Wing in the concept of behavioral subtyping, states that if S is a subtype of T, then objects of type T in a program may be replaced with objects of type S without altering any of the desirable properties of that program.
"I was thinking about it from the terms of meaning, and so I was able to say, 'It has to do with the behavior, and this subclass better behave like the superclass if you use it in an environment where the superclass is expected.'"
This principle is subtle but critical. It means that simply inheriting code isn't enough; a subclass must adhere to the behavioral contract of its superclass. Violating LSP can lead to unpredictable bugs that are notoriously difficult to trace, especially in complex inheritance hierarchies. The immediate benefit of inheritance is code reuse, but the downstream consequence of misusing it--violating LSP--is a hidden cost that erodes system integrity over time. Adhering to LSP requires a deeper understanding of specifications and behavior, a more difficult but ultimately more rewarding path that builds a more robust and predictable codebase.
The Enduring Value of Fundamental Research
Liskov's decision to remain in academia, despite the burgeoning opportunities in industry, underscores a critical aspect of long-term technological advancement: the necessity of fundamental research. While industry focuses on immediate product development, academia can explore problems without the pressure of short-term market demands. This freedom allows for the deep, foundational work that eventually underpins industry innovation.
Her observation about the "software crisis" and the subsequent development of data abstraction and modularity is a testament to this. The fact that her Turing Award was met with some skepticism--"Why did she get the Turing Award?"--stems precisely from the success of her work. Data abstraction and modularity have become so fundamental, so ingrained in the fabric of software development, that many, including her own graduate students at the time, took them for granted. They didn't remember the "before," the era of unmanageable code. This is the hallmark of truly transformative, foundational work: it changes the landscape so completely that the prior state becomes almost unimaginable.
"All that stuff was so fundamental that people thought there was no time when it hadn't already existed. So they took it for granted."
This highlights a crucial point for individuals and organizations: investing in foundational principles, even when their immediate payoff is not obvious, creates a durable advantage. The "discomfort" of rigorous design, of adhering to principles like LSP or true encapsulation, pays off years later in system stability, maintainability, and the ability to innovate on a solid base.
Key Action Items:
- Embrace True Encapsulation: Prioritize programming languages and design patterns that enforce strong encapsulation. Avoid exposing internal module details, even if it adds slight complexity in the short term. (Immediate Action)
- Define Behavioral Contracts: When designing or using inheritance, clearly define the expected behavior of superclasses and ensure subclasses adhere strictly to these contracts. This is the essence of the Liskov Substitution Principle. (Immediate Action)
- Invest in Consensus Mechanisms: For distributed systems, understand and appropriately apply consensus protocols like Paxos or Viewstamped Replication. Do not underestimate the complexity of achieving agreement across nodes. (Immediate Action)
- Prioritize Design Over Implementation: Focus on the "what" (interface, specification) before the "how" (implementation). This is the core of data abstraction and leads to more maintainable and verifiable systems. (Ongoing Investment)
- Seek Foundational Understanding: Encourage teams to understand the underlying principles of software design, not just the latest frameworks. This builds resilience against the "software crisis" recurring in new forms. (Ongoing Investment)
- Communicate the "Why": When implementing solutions that involve initial difficulty or delayed payoff (e.g., strict modularity, robust consensus), clearly articulate the long-term benefits to stakeholders to manage expectations and secure buy-in. (This pays off in 12-18 months by building team discipline and system robustness)
- Learn from History: Regularly revisit foundational computer science concepts. Understanding the problems Liskov and her contemporaries solved provides invaluable perspective on current challenges. (Ongoing Investment)