Security Failures Expose Systemic Vulnerabilities in Political Violence
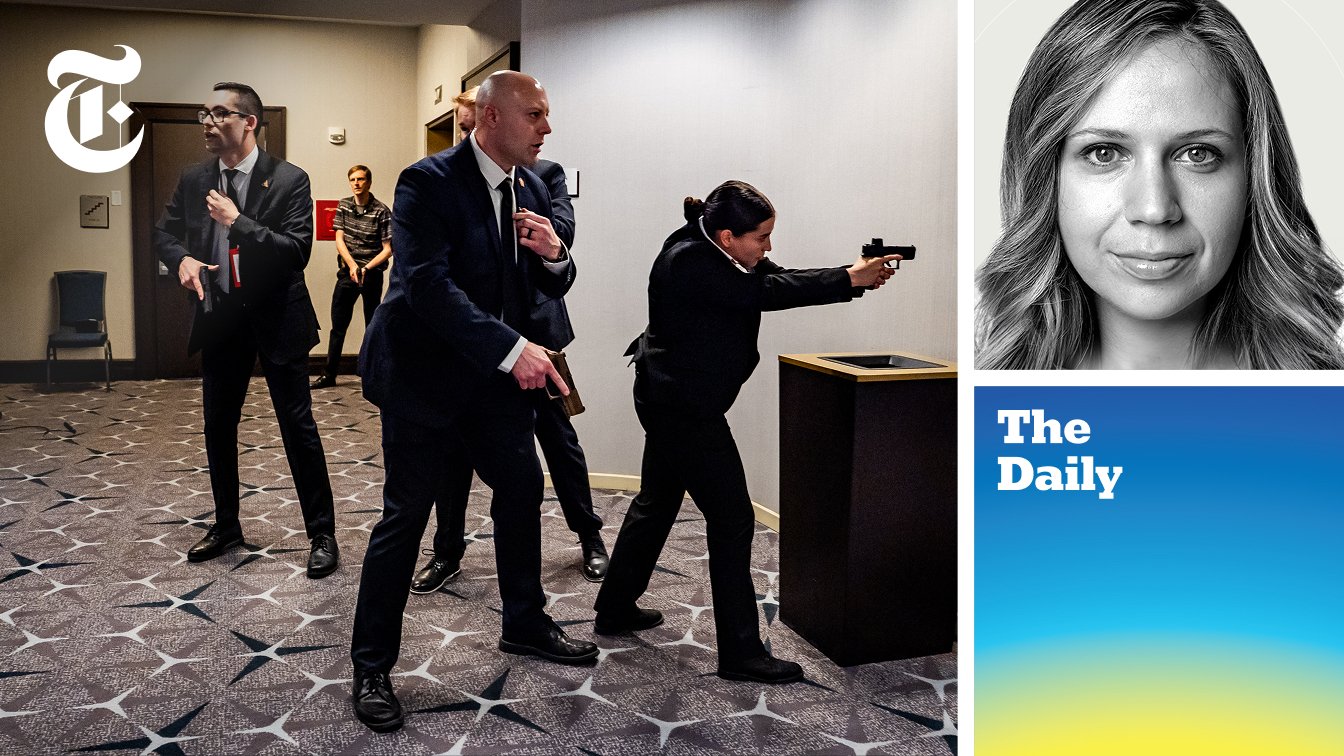
In a conversation that dissects a recent assassination attempt on President Trump at the White House Correspondents' Dinner, Devlin Barrett of The New York Times reveals the non-obvious implications of security failures and the broader landscape of political violence. This analysis is crucial for anyone involved in security, policy, or public discourse, offering a lens through which to understand how immediate threats can expose deeper systemic vulnerabilities and how conventional wisdom about security can falter when confronted with determined, albeit misguided, individuals. The narrative highlights that true security isn't just about preventing the immediate breach, but about understanding the cascading effects of perceived failures and the evolving nature of threats in a hyper-connected, often hostile, online environment. This offers a strategic advantage by moving beyond reactive measures to proactive, systems-level thinking.
The Perimeter Breached: How an Apparent Security Success Exposes Deeper Flaws
The immediate aftermath of the attempted assassination at the White House Correspondents' Dinner presented a confusing tableau of terror and relief. While the suspect, Cole Allen, was apprehended mere steps from the ballroom, the incident immediately ignited a debate: was this a security success, or a chilling failure? Devlin Barrett’s analysis, however, cuts through the surface-level reactions, suggesting that while the immediate physical breach was contained, the event exposed a fundamental misunderstanding of security perimeters and the growing challenge of political extremism. The conventional view might celebrate the swift takedown, but a systems-thinking approach reveals how this incident, by its very nature, highlights the escalating difficulty of protecting public figures and the complex interplay between online radicalization and real-world violence.
The charges filed against Allen--attempting to assassinate the president, transporting a firearm across state lines, and discharging a firearm during a crime of violence--paint a picture of a determined individual. Yet, the narrative of his apprehension is critical. He was tackled and disarmed before reaching the stairs leading to the ballroom floor. This detail, emphasized by Barrett, is where the conventional security success story begins to fray. While the immediate threat to the attendees and the President was neutralized, the fact that Allen made it past the initial security checkpoint with a shotgun visible, and that law enforcement fired shots that, while missing him, struck a Secret Service agent’s vest, suggests a perimeter that was more porous than ideal. The suspect’s own note, expressing dissatisfaction with hotel security, underscores this point. He perceived a weakness, and while the ultimate security measures prevented him from reaching his target, his initial progress suggests that the layers of protection, while present, were not as impenetrable as one might assume for such a high-profile event.
"He made it a matter of steps past the initial security screening, but he never even got onto the floor where the event was happening. He was taken down and tackled before he could even get to the stairs that led to that floor."
This observation is crucial. It implies that the "perimeter" for such an event is not a single, monolithic barrier, but a series of layered defenses. The initial checkpoint was intended to stop him, but it didn't. The agents on the scene then acted as the next layer, successfully intervening. However, the fact that a gun was fired and an agent was hit indicates that the system, while ultimately effective in preventing the assassination, experienced a near-failure. This is where the non-obvious implication emerges: the system worked, but only just. This creates a dangerous precedent, suggesting that even robust security protocols can be vulnerable to determined individuals who exploit the inherent complexities of securing large, public venues. The reliance on the next layer of defense, rather than a truly impenetrable first layer, is a systemic vulnerability that conventional security thinking might overlook in its focus on immediate threat neutralization.
Furthermore, the analysis delves into the suspect's background, noting his intelligence (a master's in computer science from Caltech) and his seemingly liberal political leanings, which stand in stark contrast to the violent act. The FBI is still unpacking his radicalization, but his note clearly indicates anger directed at the Trump administration. This points to a broader systemic issue: the challenge of identifying and mitigating threats stemming from online radicalization. The sheer volume of online threats, as Barrett notes, creates a "sea of hostility" that law enforcement must navigate. This digital deluge complicates traditional threat assessment, making it harder to distinguish between idle keyboard warriors and individuals like Allen, who translate online grievances into real-world action. The system's inability to effectively filter or intercept this escalating online anger before it manifests physically is a significant downstream consequence.
"There's sort of a sea of hostility out there online, a sea of angry, threatening language that makes it harder and more time-consuming to figure out who is really dangerous and who is just sort of a keyboard commando."
This highlights a critical failure in the information-processing aspect of security. The system is overwhelmed by noise, and the signal--the genuine threat--can be lost. The conventional approach, focused on physical security at the event, fails to adequately address the upstream problem of radicalization. This delay in identifying and intervening with individuals like Allen creates a cascading effect, where the security apparatus is forced into a reactive posture, relying on the final layers of defense rather than preventing the threat from materializing in the first place. This is a classic example of how a system designed for a predictable threat landscape can be outmaneuvered by a more fluid and insidious form of radicalization. The true competitive advantage in security, therefore, lies not in having more guards at the door, but in developing systems that can effectively process and act upon the deluge of online information to identify and neutralize threats before they reach the perimeter.
The discussion also touches upon the broader trend of heightened political violence. While Barrett cautions against definitively stating there's more political violence, he acknowledges the increase in threats and the blurring lines of what constitutes "political violence." The act at the Correspondents' Dinner, while aimed at the President, occurred in a context of other attacks on public figures and institutions. This suggests a systemic shift where public gatherings, even those symbolizing democratic processes, are increasingly viewed as potential targets. The fear generated by such events, even when the immediate threat is contained, has a chilling effect on public life. The fact that attendees at a high-profile event felt more endangered than ever, despite the security presence, underscores the psychological impact of these incidents and the erosion of a sense of safety in public spaces. This is a long-term consequence that extends beyond the immediate security of any single event, impacting the broader health of democratic engagement.
The Unseen Costs of a "Solved" Problem
-
The Illusion of Perimeter Security: The incident at the White House Correspondents' Dinner, while resulting in the suspect's swift apprehension, revealed that the perceived impenetrability of security perimeters can be a dangerous illusion. The fact that an armed individual made it past initial checkpoints with visible weaponry, even if tackled before reaching the main event, suggests a system that relies heavily on subsequent layers of defense rather than a truly robust initial barrier. This downstream effect means that even successful apprehensions can mask underlying vulnerabilities, creating a false sense of security.
-
The Digital Radicalization Deluge: Devlin Barrett highlights the overwhelming volume of online threats as a significant challenge for law enforcement. This "sea of hostility" makes it increasingly difficult and time-consuming to identify genuine threats from mere online posturing. The consequence is a system that is reactive, forced to sift through vast amounts of data rather than proactively identifying individuals on a dangerous trajectory. This upstream failure means that by the time a threat becomes physically manifest, the system has already lost valuable time and resources.
"There's sort of a sea of hostility out there online, a sea of angry, threatening language that makes it harder and more time-consuming to figure out who is really dangerous and who is just sort of a keyboard commando."
-
The Shifting Definition of Political Violence: The conversation grapples with the increasing ambiguity surrounding political violence. While direct assassination attempts on leaders are a clear measure, the inclusion of acts motivated by political grievances, even if targeting non-political individuals or institutions, broadens the scope of concern. This systemic shift means that security apparatuses must contend with a wider array of potential threats, many of which may not fit traditional profiles. The consequence is a more complex and resource-intensive security environment.
-
The Psychological Impact on Public Life: Even when security measures successfully prevent harm, incidents like this have a profound psychological impact. Attendees at the Correspondents' Dinner reported feeling more endangered than ever before. This suggests that the perception of security is as critical as its reality. When public figures and ordinary citizens alike feel increasingly vulnerable, it can have a chilling effect on participation in civic life and public discourse, a long-term consequence that undermines democratic engagement.
-
The Hotel as a Vulnerability: The specific venue, a functioning hotel with a ballroom, raises questions about the suitability of such locations for high-security events. While the suspect was apprehended before reaching the ballroom, his ability to access the hotel and progress through initial checkpoints highlights the inherent security challenges of mixed-use spaces. This suggests that conventional security models may need to adapt to the realities of modern infrastructure, where clear separation between public and secure areas is often blurred.
Key Action Items
-
Immediate Actions (0-3 months):
- Enhance Online Threat Monitoring: Law enforcement agencies should invest in advanced AI and analytical tools to better filter and prioritize online threats, distinguishing genuine danger from mere rhetoric.
- Review Hotel Security Protocols: For events in mixed-use venues, conduct rigorous threat assessments specifically for the hotel's public areas, not just the event space itself.
- Cross-Agency Information Sharing Drills: Conduct simulated exercises where different law enforcement agencies (local, federal, intelligence) practice sharing and acting upon information regarding potential threats to public figures.
- Public Communication Strategy Refinement: Develop clear, consistent communication protocols for responding to security incidents to manage public perception and reduce panic.
-
Longer-Term Investments (6-18 months+):
- Develop Proactive Radicalization Intervention Programs: Invest in research and pilot programs aimed at identifying and intervening with individuals exhibiting signs of online radicalization before they escalate to physical threats. This requires a shift from reactive security to proactive social and psychological support.
- Re-evaluate Perimeter Security Models: Explore and implement more innovative perimeter security strategies that go beyond traditional checkpoints, potentially integrating advanced surveillance, behavioral analysis, and more dynamic threat response. This requires embracing discomfort now for future advantage.
- Invest in Secure Event Infrastructure: Advocate for and invest in purpose-built secure venues for critical government and public events, reducing reliance on compromised mixed-use spaces. This is an investment that pays off in enhanced, long-term safety.