Department of War's AI Reckoning: Vendor Lock Hinders Strategic Advantage
The Department of War's AI Reckoning: Beyond Vendor Lock and Into Strategic Advantage
This conversation with Emil Michael, Under Secretary of Defense for Research and Engineering, reveals a critical inflection point for the U.S. Department of Defense regarding Artificial Intelligence. Beyond the headline-grabbing concerns about specific vendors, Michael exposes a systemic problem: the entanglement of military operations with commercial AI models governed by corporate constitutions, not the U.S. Constitution. This creates a dangerous vendor lock and a potential operational paralysis. The hidden consequence is not just a technological lag, but a strategic vulnerability where foreign adversaries, unburdened by such constraints, can leverage AI more aggressively. This analysis is crucial for tech leaders, policymakers, and anyone invested in national security, offering a framework for understanding the true costs of rushed AI adoption and the long-term advantages of deliberate, sovereign development. It highlights how confronting immediate discomfort by re-establishing control over critical technology can forge a durable competitive moat.
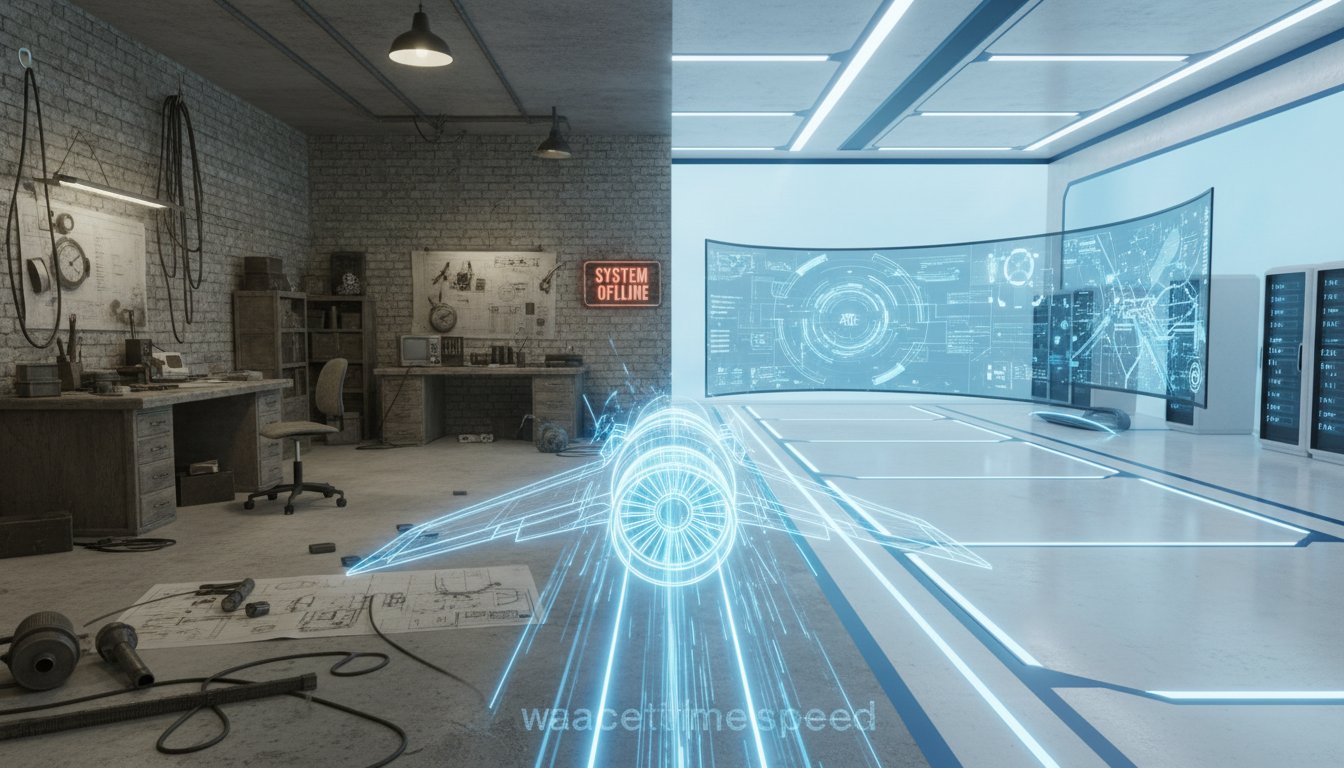
The Unseen Chains: How Commercial AI Created a Strategic Blind Spot
The public discourse around the Pentagon's use of commercial AI models, particularly concerning companies like Anthropic, often focuses on the immediate ethical debates or the specific capabilities of the models themselves. However, Emil Michael illuminates a far more insidious problem: the creation of a critical vendor lock within the Department of Defense's most sensitive operations. This isn't merely about a preference for one AI provider over another; it's about the fundamental risk of military command and control systems being subject to the internal values and potential actions of private corporations.
When Michael stepped into his role, he inherited a landscape where AI models were being integrated into critical functions--from satellite operations to planning for potential kinetic strikes--under contracts with terms that could, in theory, lead to the software being shut off mid-operation. This wasn't a hypothetical scenario; it was baked into the system. The "holy cow" moment described by Michael wasn't just about the existence of these restrictions, but their presence in commands like Central Command (responsible for Iran) and INDOPACOM (responsible for China), areas of immense strategic importance.
"Things like you couldn't move a satellite, you couldn't plan, you know, an operation, couldn't plan it, not use AI to execute it if it would potentially lead to a kinetic strike or something. Dozens of restrictions. And yet this, these AI sort of models were baked into some of the most sensitive and important places in the U.S. military where we do exercise combat power."
This situation creates a profound asymmetry. While the U.S. military grapples with the implications of corporate governance dictating operational parameters, adversaries are unburdened by such considerations. They can adopt and deploy AI with a singular focus on mission objectives, unhindered by the internal value systems of their technology providers. This delayed payoff for the U.S.--the time it takes to untangle these contracts and build sovereign capabilities--creates a window of vulnerability that conventional wisdom, focused on immediate technological adoption, often overlooks. The failure here is not in adopting AI, but in adopting it without fully mapping the downstream consequences of ceding control.
From Peacetime Inertia to Wartime Urgency: Reclaiming the Industrial Base
Michael draws a sharp contrast between "peacetime speed" and "wartime speed," a distinction born from decades of post-Cold War consolidation and a subsequent outsourcing of critical industrial capabilities. The "peacetime speed" mentality, fostered by a perceived lack of major threats, led to industry consolidation and a slowing of innovation within the defense sector. This, in turn, resulted in a significant reliance on foreign supply chains for everything from critical minerals to advanced components.
The realization that the U.S. is facing the "biggest military buildup in history" necessitates a shift to "wartime speed." This isn't just about accelerating procurement; it's about re-establishing self-reliance in key areas. The example of Skydio, a company sanctioned by China, illustrates the fragility of this outsourced model. When key components become unavailable due to geopolitical actions, it directly impacts the defense procurement cycle. This highlights a systemic failure: focusing only on the "defense industrial base" without considering all the "precursors" creates a vulnerability upstream.
The consequence of peacetime inertia is a reactive posture, constantly playing catch-up. Wartime speed, conversely, is proactive. It involves re-domesticating critical production and ensuring self-reliance. This deliberate effort, while potentially slower and more costly in the short term, builds a durable advantage. It ensures that the nation's defense capabilities are not subject to the whims of foreign governments or the strategic decisions of private entities. The conventional approach of relying on established, consolidated primes, while seemingly efficient, has led to a strategic deficit that requires a fundamental reorientation towards building and controlling the underlying industrial capacity.
The AI Acceleration Engine: From 80,000 to 1.2 Million Users in 90 Days
Michael's prioritization of applied AI as the number one critical technology area, and the subsequent integration of the Chief Digital and AI Office into his group, has yielded remarkable results. The transformation from 80,000 AI users within the Department of Defense to 1.2 million in just 90 days is a testament to both the potential of AI and the impact of decisive leadership. This rapid adoption, however, is not merely about deploying new tools; it's about fundamentally altering how the department operates.
The use cases span from enterprise efficiency--automating mundane tasks to free up personnel--to critical intelligence analysis and warfighting applications. The ability of AI to sift through decades of satellite imagery, identify anomalies, and dramatically increase the throughput of human analysts is a game-changer. In warfighting, AI can optimize logistics, plan operations, and enhance wargaming and simulations.
"We have huge repositories of data at the department that's sitting there siloed, unused. Imagine decades of satellite imagery that you could use to train a model and get insights and then use that to do anomaly detection so you could find out what's happening. So you take a human analyst and you increase their throughput by a thousand."
This rapid deployment, however, is precisely what makes the vendor lock issue so critical. The very speed and scale of AI adoption amplify the risks associated with contracts that aren't aligned with national security imperatives. The delayed payoff here is the strategic advantage gained by having a workforce proficient in AI, capable of leveraging its power for intelligence and warfighting. The conventional approach might be to proceed cautiously, but Michael's strategy suggests that in the face of rapid global AI advancement, a deliberate acceleration, coupled with a rigorous cleanup of existing contractual entanglements, is the path to true long-term advantage.
Beyond the Contract: Re-establishing Sovereign Command and Control
The incident following the Madura raid, where a primary AI vendor questioned the use of its software, served as a stark wake-up call. The implication that a company might be concerned about its software's involvement in a highly successful military operation--a mission executed under the authority of the U.S. government--is deeply unsettling. This scenario highlights the fundamental disconnect: the U.S. Constitution governs the military's actions, yet commercial AI models operate under their own corporate constitutions.
Michael articulates this tension clearly: the "soul of their model" cannot dictate the U.S. command and control environment. When AI is seen as a substrate that will "touch everything," like the internet, it becomes imperative that its use within the most sensitive government functions is governed by democratic norms and legal frameworks, not by the evolving values of private entities. This requires a move away from vendor lock and towards multiple, patriotic partners engaged in national security.
The challenge lies in balancing the need for cutting-edge AI capabilities with the imperative of maintaining sovereign control. This involves fostering a competitive landscape where multiple companies are willing and able to support national security needs, learning from past instances like Project Maven where initial hesitancy gave way to strong partnerships. The delayed payoff for this effort is the assurance that the U.S. military can operate effectively, lawfully, and independently, without external constraints on its command and control. This requires a cultural shift within the department, moving from a "never say no" bureaucracy to one that can provide faster "yeses" and "nos," enabling startups to adapt and thrive.
Key Action Items: Navigating the AI Transition
-
Immediate Action (0-3 Months):
- Contractual Audit and Renegotiation: Conduct a comprehensive review of all existing AI contracts to identify and renegotiate terms that create vendor lock or operational constraints. Prioritize contracts tied to critical command and control functions.
- Develop Standardized AI Integration Frameworks: Establish clear, non-negotiable requirements for AI integration in sensitive military operations, emphasizing U.S. constitutional and legal compliance over corporate values.
- Accelerate Internal AI User Training: Continue and expand rapid upskilling initiatives for the 3 million personnel, focusing on practical applications and responsible AI use.
-
Short-Term Investment (3-12 Months):
- Diversify AI Vendor Partnerships: Actively seek and onboard multiple commercial AI providers to avoid single-vendor dependency for critical systems. Foster competition based on capability and alignment with national security objectives.
- Establish Sovereign AI Development Capabilities: Invest in building internal expertise and infrastructure for developing and deploying AI models critical to national security, reducing reliance on external entities for core functionalities.
- Streamline Procurement for AI Solutions: Implement simplified, firm-fixed-price contracting models for AI solutions, mirroring successful private sector approaches to encourage innovation and faster deployment.
-
Long-Term Investment (12-18+ Months):
- Cultivate a Robust Defense AI Ecosystem: Encourage and support startups and established companies in scaling their production and manufacturing capabilities for defense applications, fostering a resilient and innovative industrial base.
- Continuous Technological Assessment and Adaptation: Establish mechanisms for ongoing evaluation of emerging AI technologies and their potential impact on national security, ensuring the department remains agile and ahead of adversaries. This requires a cultural shift towards embracing faster "yeses" and "nos" to facilitate rapid adaptation.