AI Accelerates Vulnerability Lifecycle, Demanding Security Adaptation Now
The AI Tsunami is Here: Why Mythos and Its Descendants Demand Immediate Action
The industry is facing an unprecedented shift, not just in the capabilities of AI for finding software vulnerabilities, but in the speed at which these discoveries can be weaponized. This conversation reveals that the era of AI-driven bug hunting has arrived, presenting a stark choice: adapt now or face an avalanche of exploits. The non-obvious implication is that traditional security models, built for a slower, human-centric world, are fundamentally unprepared for this new reality. Security leaders, developers, and C-suite executives who grasp the systemic implications of this acceleration will gain a critical advantage in navigating the coming storm. Those who dismiss it as hype risk being overwhelmed by a wave of attacks that outpace their ability to respond.
The Imminent Tsunami: AI's Assault on Software Security
The conversation around Project Mythos, an AI capable of autonomously discovering and exploiting software vulnerabilities, is not hype; it is a harbinger of a fundamental shift in cybersecurity. The evidence is mounting: Microsoft is reportedly purchasing its own bugs, a disgruntled developer is weaponizing zero-days, and even well-established projects like VeraCrypt and Wireshark have faced disruptions due to account suspensions. But the most compelling evidence comes from the cybersecurity industry itself. A collective of security professionals, including prominent figures like Bruce Schneier and Google's CISO, have co-authored a document warning of an impending "tsunami" of AI-driven exploits. This isn't a future threat; it's happening now.
The core of the issue lies in the radical acceleration of the vulnerability lifecycle. Traditionally, discovering a significant bug, developing an exploit, and then seeing it weaponized took considerable time and expertise. AI, as exemplified by Mythos and its ilk, collapses this timeline to mere hours. This creates a profound asymmetry: attackers can discover and exploit vulnerabilities faster than organizations can patch them.
"The asymmetry this creates is structural. AI lowers the cost and skill floor for discovering and exploiting vulnerabilities faster than organizations can patch them."
This statement from the industry expert paper cuts to the heart of the problem. It means that the skills and resources previously required to be a sophisticated attacker are now accessible to a much wider pool of actors. The "script kiddie" of yesterday could become the highly effective exploiter of tomorrow, simply by leveraging AI tools. This isn't about theoretical future capabilities; it's about the immediate reality of attackers gaining disproportionate benefit because current patch cycles and risk metrics were not designed for this speed.
The Disgruntled Developer: A Symptom of a Broken System
The story of the "disgruntled developer" who leaked Windows zero-days highlights a critical downstream effect of the current system. While Microsoft claims to support coordinated vulnerability disclosure, the researcher's account paints a picture of a broken process, leading to anger and the premature release of exploits. This incident, while seemingly isolated, reveals a systemic issue: the current methods of handling vulnerability disclosures are failing to keep pace with the discovery rate, potentially incentivizing researchers to bypass official channels.
The technical details of the "Red Sun" exploit are a testament to the ingenuity that can be unleashed, even when fueled by frustration. It leverages Windows Defender's own behavior to escalate privileges, demonstrating how even defensive tools can become vectors for attack when exploited by sophisticated techniques. The fact that this vulnerability, even after a major patch Tuesday, was being actively exploited in the wild underscores the urgency.
"Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible. We also support coordinated vulnerability disclosure..."
This quote, from Microsoft, stands in stark contrast to the researcher's experience. While the company's stated commitment is laudable, the researcher's claim of being "told personally by them that they will ruin my life" suggests a disconnect between policy and practice. This disconnect can have severe consequences, pushing valuable security insights into the hands of malicious actors rather than facilitating their secure remediation.
The Recaptured Domain: The Internet's Aging Infrastructure Cracks
The issue of recaptured domain names, where abandoned domains are re-registered and used to control previously installed software, is another stark illustration of the internet's aging infrastructure failing to cope with modern threats. The case of the "Dragon Boss Solutions LLC" adware, which included an "antivirus killer" and silently deployed payloads, is particularly alarming. When the company's update domains were abandoned, researchers from Huntress were able to re-register them, gaining control over tens of thousands of infected endpoints.
This scenario is a perfect example of a second-order negative consequence. The initial software, while perhaps merely an annoyance (a PUP, or Potentially Unwanted Program), contained a mechanism for silent updates and the disabling of security software. When the publisher disappeared, the dormant infrastructure became a ready-made backdoor.
"Huntress warns that while the malicious tool currently uses an AV killer, the mechanism to introduce far more dangerous payloads into infected systems is in place and could be leveraged at any time to escalate the attacks."
This highlights the delayed payoff of poor design and abandonment. The immediate "benefit" for the adware publisher was ad revenue, but the long-term consequence of their disappearance created a massive security risk for thousands of organizations, including critical infrastructure and educational institutions. The fact that this was discovered by ethical researchers highlights the potential for malicious actors to exploit similar situations, turning what was once a nuisance into a potent weapon. The internet's design, never intended for this scale of automated, persistent communication and update mechanisms, is showing its age.
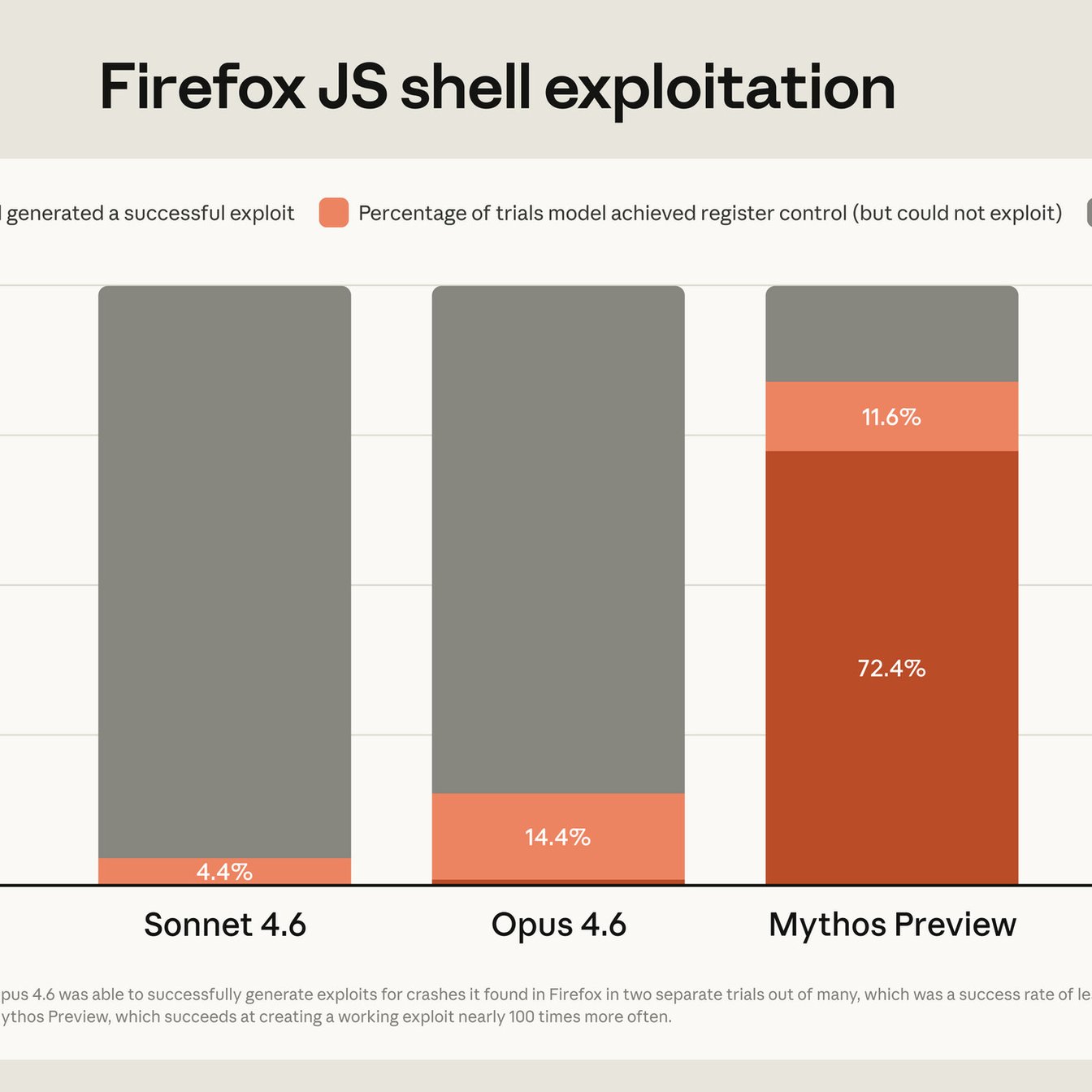
The Mythos Revelation: A Y2K Moment for Security
The confirmation from Mozilla that they used Mythos to discover 271 bugs in Firefox, a highly tested and currently shipping product, is a pivotal moment. It validates the claims that AI is not just finding bugs, but finding categories of bugs that human analysis and even prior automated tools missed. This is the "Y2K moment" for cybersecurity: a period of intense, potentially chaotic discovery followed by a necessary, albeit difficult, transition.
The experts' paper emphasizes that this is a "transitory moment." While the current wave of AI-driven vulnerability discovery is overwhelming, it also presents an opportunity. Organizations that embrace AI defensively, using it to find and fix bugs before attackers do, will be better positioned. The key is to build the "muscle now"--the processes, tooling, and culture--to adopt AI as a core part of security operations.
"The organizations that respond well will be those that build the muscle now, the processes, the tooling, and a culture willing to adopt AI as a core part of how security gets done. The adaptability will help determine who meets the next wave on their own terms."
This insight is crucial. The immediate discomfort of re-evaluating security postures, investing in new tools, and retraining personnel will create a lasting advantage. The alternative is to be caught flat-footed by an escalating threat landscape. The window between discovery and weaponization has collapsed, and the ability to adapt quickly is paramount.
Key Action Items
-
Immediate Action (Next 1-3 Months):
- Establish an AI Security Task Force: Form a cross-functional team to assess current AI usage and risks within the organization.
- Review AI Usage Policies: Implement clear guidelines on what data can and cannot be shared with public AI models.
- Prioritize Patching: Aggressively review and accelerate patch deployment for critical systems, acknowledging that AI can shorten the exploit window.
- Enhance Vulnerability Disclosure: Re-evaluate internal processes for receiving and responding to vulnerability reports, ensuring timely and fair treatment of researchers.
- Conduct AI-Driven Threat Hunting: Begin experimenting with AI tools for proactive threat hunting and vulnerability discovery within your own environment.
-
Medium-Term Investment (3-12 Months):
- Invest in AI-Powered Security Tools: Explore and deploy AI solutions for threat detection, incident response, and vulnerability management.
- Develop AI Defense Strategies: Begin building internal capabilities to use AI defensively, mirroring attacker capabilities.
- Train Security Teams on AI: Provide comprehensive training for security professionals on AI capabilities, risks, and defensive applications.
- Review Incident Response Plans: Update incident response playbooks to account for the speed and scale of AI-driven attacks.
-
Long-Term Strategic Shift (12-24 Months):
- Integrate AI into the SDLC: Embed AI-driven security analysis into the software development lifecycle to catch vulnerabilities before deployment.
- Re-evaluate Risk Metrics: Develop new metrics that account for the accelerated threat landscape and AI's impact on attack vectors.
- Foster an AI-Adaptive Culture: Cultivate an organizational culture that embraces continuous learning and adaptation to new security paradigms.
- Explore AI-Assisted Patching: Investigate automated or AI-assisted patching solutions to reduce the time between vulnerability discovery and remediation.