The Future of Linux is Here: Insights from Planet Linux and SCALE 2026
This discussion dives deep into the evolving landscape of Linux, particularly highlighting the burgeoning influence of Nix and the broader implications of AI on software development. Beyond the surface-level excitement of new technologies, this conversation reveals a subtle but significant shift: the increasing need for reproducible, verifiable, and manageable systems in an era of AI-generated code and complex infrastructure. For developers, system administrators, and tech leaders, understanding these underlying currents offers a critical advantage in navigating the future of software creation and deployment. The true value lies not just in adopting new tools, but in grasping the systemic shifts that make them indispensable.
The Unfolding Ecosystem: Nix, AI, and the Quest for Reproducibility
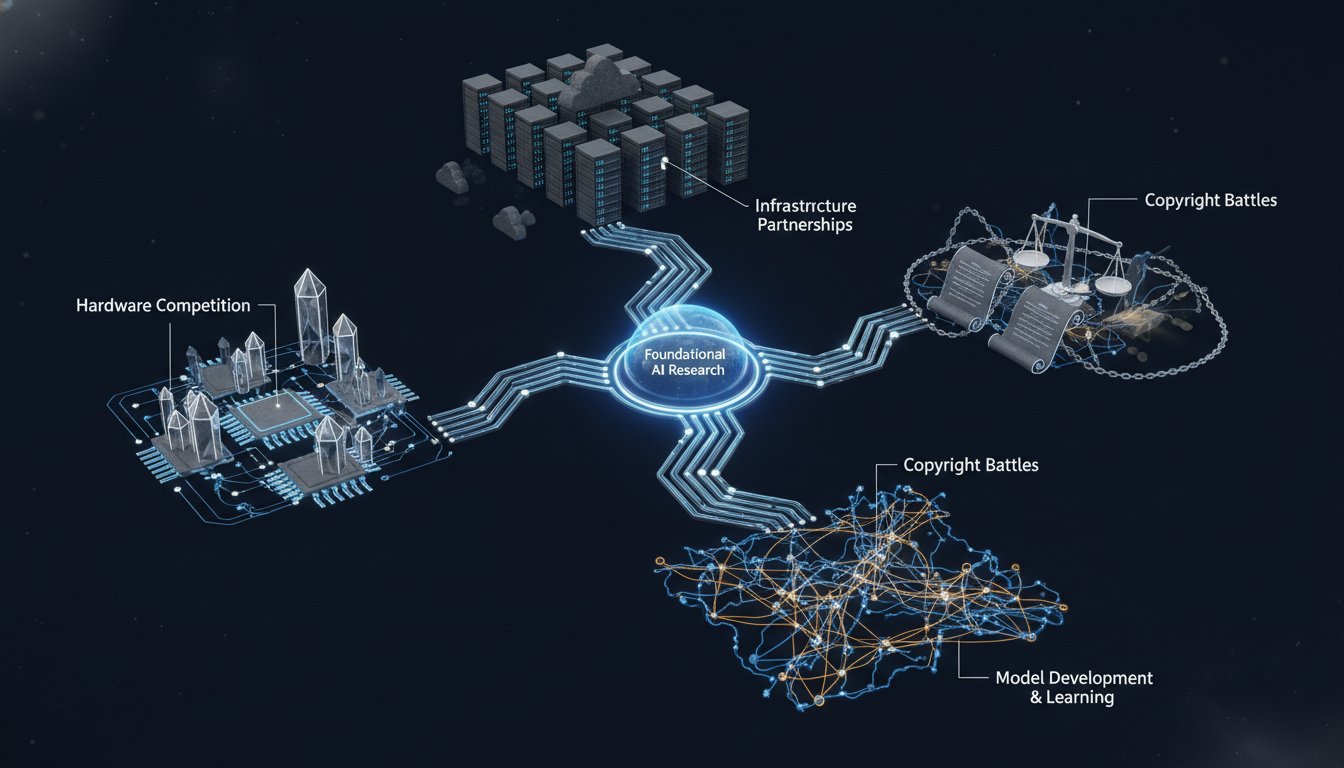
The recent Planet Linux and SCALE 2026 conferences underscored a pivotal moment in the Linux ecosystem, marked by the growing prominence of Nix and the pervasive influence of artificial intelligence. While many discussions focused on the immediate benefits of these technologies, a deeper analysis reveals a fundamental shift towards systems that prioritize reproducibility, reliability, and manageability -- qualities that are becoming increasingly crucial in the age of AI-driven development.
One of the most striking observations from the event was the synergy between Nix and the burgeoning AI landscape. As speakers discussed the rise of AI agents capable of generating code, a recurring theme emerged: the need for robust frameworks to manage and validate this automatically generated output. Nix, with its declarative approach to package management and system configuration, stands out as a potential cornerstone for bringing order to the potential chaos of AI-generated code. The ability to define, build, and deploy software in a reproducible manner is not just a convenience; it’s becoming a necessity when the source of that software can be an algorithm.
This was particularly evident in the discussions surrounding Nix's potential role in managing AI-generated code. As one speaker noted, "The LLMs need guardrails and they need the ability to know when they've broken the system or when the system is operational." Nix, by providing a deterministic and reproducible environment, can serve as these essential guardrails. The implication is that as AI becomes more integrated into the development lifecycle, tools like Nix, which guarantee consistent builds and deployments, will become not just beneficial but indispensable. This shift suggests a future where managing the infrastructure and dependencies for AI-generated code will be as critical as the code itself.
A key takeaway from the conference was the concept of "vibe coding" versus robust development. While AI can rapidly generate snippets of code for quick tasks -- akin to "paper plates" for software development -- the need for durable, well-managed, and traceable code remains paramount for critical systems. The discussion highlighted the potential for AI to exacerbate existing challenges in software maintenance and contribution if not managed properly. As one speaker questioned, "Do we become the guardrails or do we get replaced by people creating software for themselves and not sharing it back?" This points to a potential bifurcation: AI-assisted development for ephemeral tasks versus meticulously managed, version-controlled, and community-contributed code for long-term projects.
Nix's role extends beyond just managing code; it's about managing the entire software supply chain. The concept of "provenance" -- understanding the origin, dependencies, and build process of software -- was frequently mentioned. With AI-generated code, provenance becomes even more critical. Tools like Nix, which can attach metadata about build processes, dependencies, and even licenses, offer a way to bring transparency and accountability to AI-generated software. This ability to trace the lineage of code is crucial for security, compliance, and debugging, especially when dealing with potentially opaque AI models.
The conference also touched upon the practical application of Nix in bridging different ecosystems. The demonstration of using Nix tools to package software typically found in Debian-based systems, like bcachefs, onto an Ubuntu environment highlighted the interoperability and flexibility Nix offers. This ability to "do surgery" on binaries, making them portable across different distributions, showcases Nix's potential to break down traditional silos and foster a more unified Linux experience. This cross-pollination is vital as the broader software ecosystem increasingly relies on diverse and interconnected components, many of which will likely be influenced or generated by AI.
Furthermore, the discussions around Nix's adoption in enterprise settings, including government and healthcare, underscore its growing maturity and reliability. The challenges faced by organizations in ensuring compliance and security are driving the adoption of robust systems like Nix. As one speaker noted, "Our auditors are kind of scared of it [Nix], and this is really helping a lot of places to take advantage of it and be comfortable with it." This suggests that the very rigor and predictability that Nix offers are becoming essential differentiators in sensitive industries, positioning it as a foundational technology for future secure and scalable systems, especially those integrating AI components.
"The LLMs need guardrails and they need the ability to know when they've broken the system or when the system is operational."
This quote encapsulates the core challenge: managing the output of increasingly autonomous systems. Nix, with its declarative and reproducible nature, offers a framework to impose order and predictability on this potentially chaotic landscape.
"Do we become the guardrails or do we get replaced by people creating software for themselves and not sharing it back?"
This question highlights a critical juncture for the open-source community. As AI tools become more capable of generating standalone solutions, the collaborative spirit of open source faces a new test. Nix, by facilitating reproducible builds and clear dependency management, can empower developers to contribute and manage complex, AI-assisted projects effectively.
"The way the way that I've been looking at it and I've been talking to folks inside of Nix outside of Nix is I think the the more I'm seeing where the industry is going is that I would love for it to be a fact right so to your point about the vision for for Nix and in the modern as you'll see is that Nix can be the pure way that we actually are able to derive the packages and the baseline infra for what we're building regardless of if it's led by a human by an agent by a model it doesn't matter right"
This statement underscores the potential for Nix to become a universal standard for managing software artifacts, irrespective of their origin, be it human-written or AI-generated. Its inherent design principles align perfectly with the need for verifiable and reproducible systems in the age of AI.
Key Action Items:
- Embrace Declarative Configuration: Begin migrating key infrastructure and application deployments to a declarative model, similar to Nix, to enhance reproducibility and version control. Start with a single critical service or development environment.
- Investigate Nix Ecosystem: Allocate time to explore Nix and its package manager. Understand its concepts of derivations, the Nix store, and flakes. Consider using Nix for managing development environments for new projects. (Immediate to 3 months)
- Prioritize Reproducibility: When evaluating new tools or workflows, prioritize those that offer reproducible builds and deployments. This is crucial for managing the complexities introduced by AI-generated code. (Ongoing)
- Explore AI Integration with Caution: Experiment with AI coding assistants and tools, but always validate their output rigorously. Understand how to integrate these tools within a controlled, reproducible environment like Nix. (Ongoing)
- Develop Provenance Strategies: Implement practices to track the origin and dependencies of software components, especially those generated or assisted by AI. This involves understanding metadata and build history. (6-12 months)
- Contribute to Open Source Standards: Engage in discussions and contribute to the development of standards for AI-generated code and open-source AI models, focusing on aspects like licensing, security, and provenance. (Long-term)
- Build for Resilience: Focus on building systems that are resilient to change and easy to manage, even as underlying technologies like AI evolve rapidly. Nix’s immutable nature and declarative approach are key enablers here. (12-18 months for significant impact)